
Microsoft has launched a new open-source project that aims to add to Windows the benefits of eBPF, a technology first implemented in Linux that allows attaching programs in both kernel and user applications.
The advantages associated with eBPF (Extended Berkeley Packet Filter) range from network performance and security to event analysis and observability.
eBPF technology allows a user-supplied program to run isolated (sandboxed) inside the kernel of an operating system at a specific event, a hook point like a system call, a function entry/exit, kernel tracepoints, or network events.
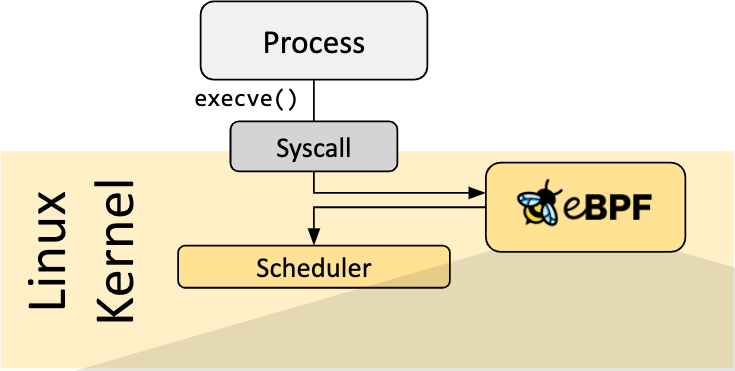
Being attached to a pre-defined hook and working at such low level gives an eBPF program the possibility to inspect in real time data that has not been altered by malicious activity.
For these reasons, eBPF programs are particularly useful for filtering, monitoring, and analysis tasks that have applications in the networking and security fields.
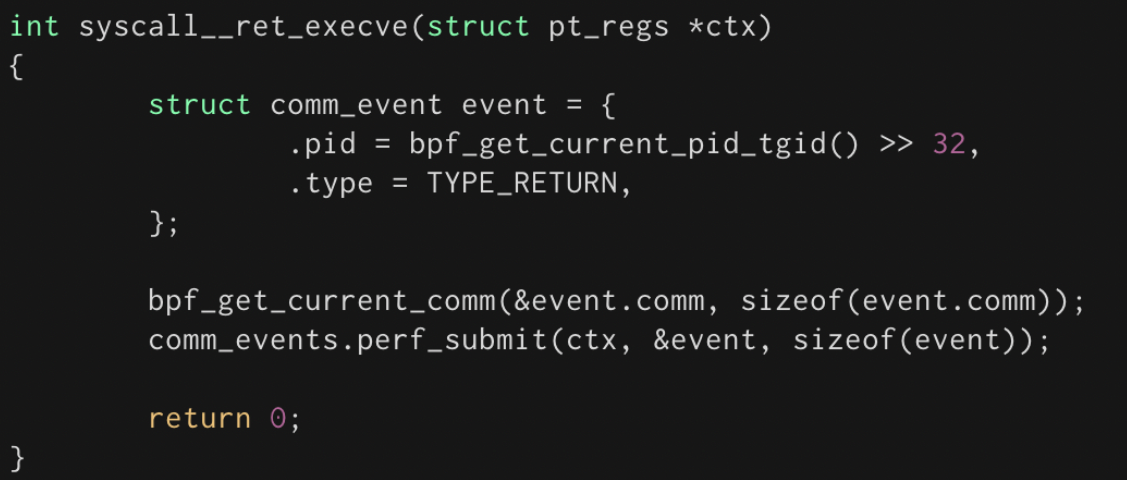
They are also suitable for debugging purposes on live systems as eBPF programs can access kernel data structure and there is no need to recompile the kernel for them to run.
eBPF development gets Windows chapter
Microsoft’s effort builds on the work of the eBPF community by adding a compatibility layer that turns existing eBPF open-source projects into submodules that can work on top of Windows 10 and Windows Server 2016 and later.
“The ebpf-for-windows project aims to allow developers to use familiar eBPF toolchains and application programming interfaces (APIs) on top of existing versions of Windows” - Microsoft
An architectural view of the project shows that an eBPF program can use toolchains to generate eBPF bytecode in a variety of languages so any application can use it and even be fed into the Windows Netsh command-line tool, with the help of a shared library.
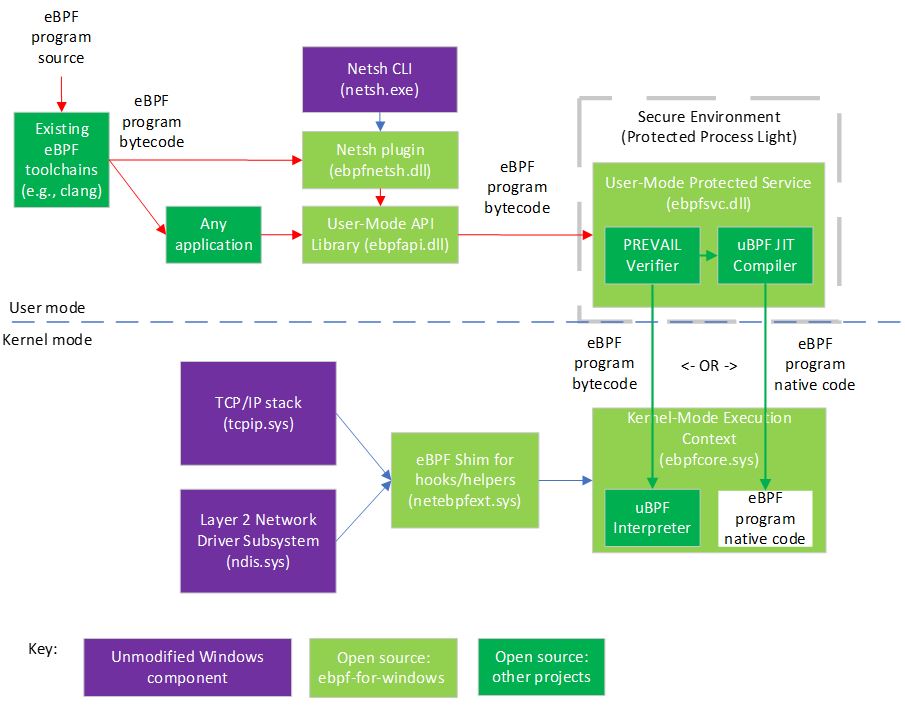
As seen in the image above, Microsoft uses the PREVAIL eBPF verifier hosted in a user-mode protected process, and IO Visor’s uBPF running in kernel-mode execution context, to check the legitimacy of the resulting bytecode and to execute an eBPF program on top of Windows.
Microsoft explains that “eBPF programs installed into the kernel-mode execution context can attach to various hooks to handle events and call various helper APIs exposed by the eBPF shim, which internally wraps public Windows kernel APIs, allowing the use of eBPF on existing versions of Windows.”
Currently, there are only two hooks available - XDP and socket bind - both related to networking. However, Microsoft expects more to be added in the future, to cover other areas as well.
With this project, Microsoft wants to “port” to its operating system the hooks and helpers written for Linux that have an application to Windows.
“Similarly, the eBPF for Windows project exposes Libbpf APIs to provide source code compatibility for applications that interact with eBPF programs” - Microsoft
The ebpf-for-windows project is still at the beginning and the long-term purpose is to “bring the power of eBPF to Windows users” and to become part of the larger eBPF community that would also guide its development.
A tutorial on how to author an eBPF program and make it run on Windows is available here.
8 Common Threats in 2025
While cloud attacks may be growing more sophisticated, attackers still succeed with surprisingly simple techniques.
Drawing from Wiz's detections across thousands of organizations, this report reveals 8 key techniques used by cloud-fluent threat actors.









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now