The team behind Exploit, a major cybercrime forum used by ransomware gangs to hire affiliates and advertise their Ransomware-as-a-Service (RaaS) services, has announced that ransomware ads are now banned and will be removed.
The move follows the announcement made by the XSS Russian-speaking hacking forum yesterday about ransomware topics being permanently banned.
Exploit says the decision was taken because ransomware groups attacking targets indiscriminately attracts "a lot of attention."
Besides the ban, the forum admins will also remove all topics related to ransomware operations and all affiliate programs.
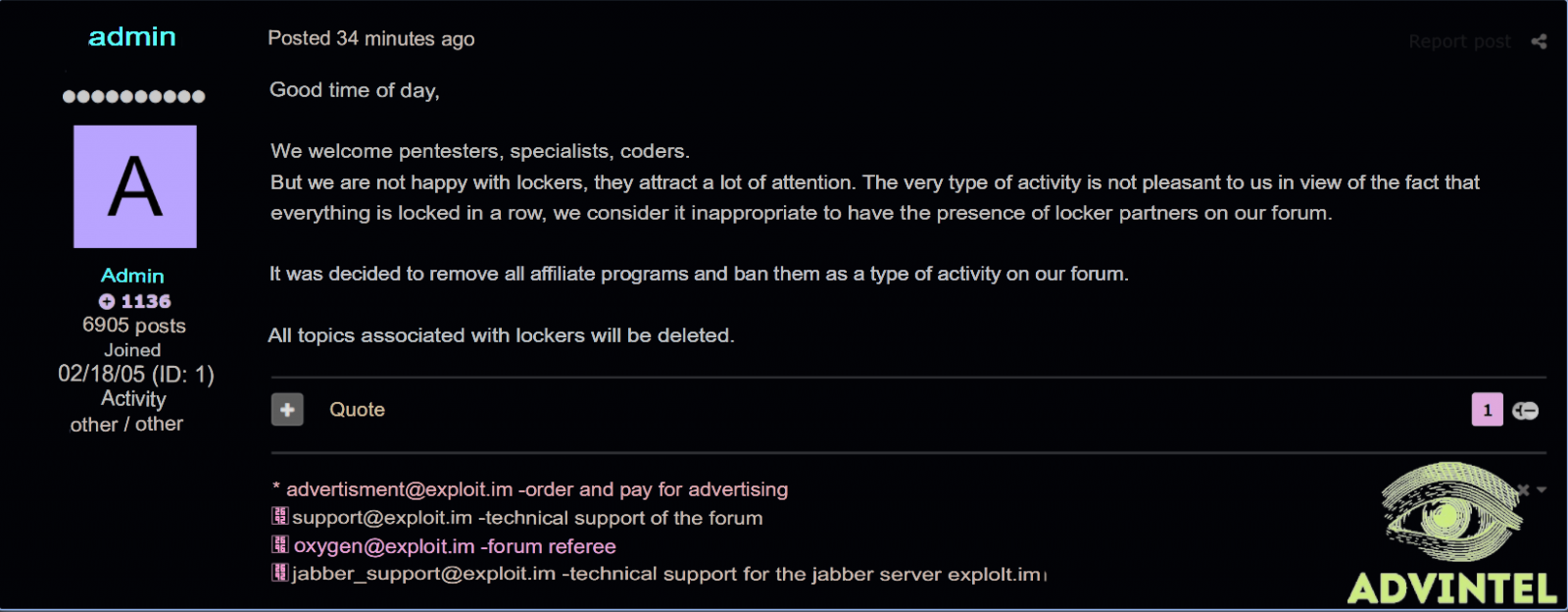
The complete statement, provided and translated by Advanced Intel's Yelisey Boguslavskiy and Vitali Kremez, is available below.
Good day,
We are glad to see pentesters, malware specialists, coders, but we are not happy with lockers - they attract a lot of attention. This type of activity is not good to us in view of the fact that networks are locked indiscriminately we do not consider it appropriate for RaaS partner programs to be present on our forum.
It was decided to remove all affiliate programs and prohibit them as a type of activity on our forum.
All topics related to lockers will be deleted.
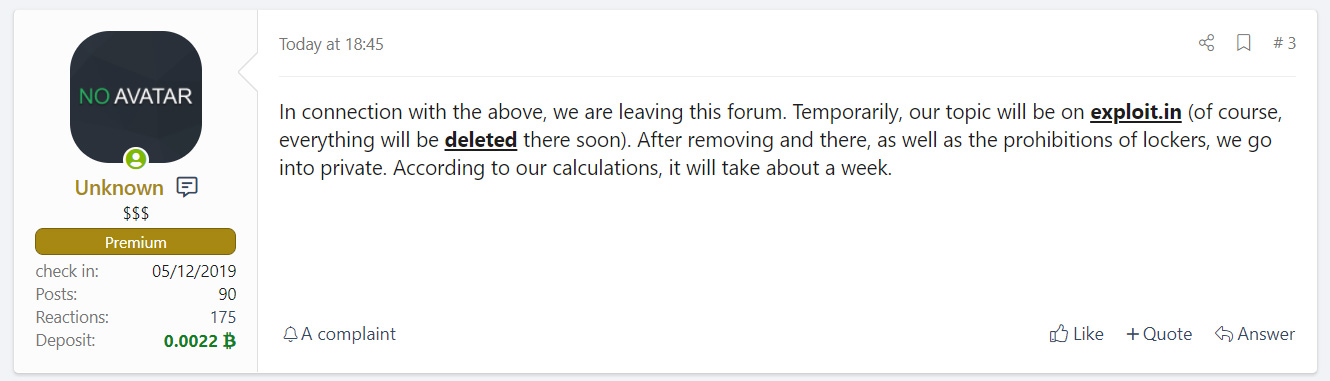
Ransomware gangs have already expressed their disapproval after XSS posted their decision to ban them from the forums. For instance, the REvil ransomware gang announced that the operation will move to Exploit.
REvil added that the gang will move onto a private platform within a week. However, they will have to be a lot faster since Exploit also banned ransomware topics to evade unwanted attention from US law enforcement.
With more cybercrime and hacking communities pushing ransomware operations off their platforms, it remains to be seen how and if RaaS gangs will keep promoting their activities and recruiting new affiliates.
DarkSide shuts down RaaS operation
Exploit and XSS respond to increased pressure on RaaS gangs who have previously used the two forums, including REvil, LockBit, DarkSide, Netwalker, and Nefilim.
This is a direct result of them landing in the crosshairs of law enforcement after DarkSide ransomware's attack on Colonial Pipeline, which disrupted the US fuel pipeline's operation.
The attack was also addressed by the White House in this week's national security briefings and prompted a regional emergency declaration affecting 17 states and the District of Columbia.
After the incident, the DarkSide ransomware gang posted a "press release" stating that they are apolitical and that they will start vetting all targets before attacks.
Colonial Pipeline has since restored all pipeline operations after reportedly paying DarkSide almost $5 million worth of cryptocurrency for a decryption key.
UNKN, a threat actor known as the public-facing representative of rival ransomware gang REvil, also announced today that the DarkSide RaaS operation shut down after losing access to public data leak site, payment servers, and CDN servers "at the request of law enfocement agencies," and having their cryptocurrency transferred to an unknown wallet.
DarkSide confirmed UNKN's claims in a message sent to their RaaS affiliates saying that they decided to close their operation "due to the pressure from the US" and losing access to their public-facing servers.
After DarkSide's shutdown, REvil announced new restrictions on targets that can be encrypted by affiliates.
UNKN said that REvil affiliates are now required to obtain permission before targeting an organization and that:
1. Work in the social sector (health care, educational institutions) is prohibited;
2. It is forbidden to work on the gov-sector (state) of any country;
Update: Added info on DarkSide RaaS shutdown and REvil's new targeting restrictions.



Comments
yawnshard - 2 years ago
Even now you should put more news articles on that disgusting cybercrime forum. Give them all the unwanted attention they hate!