Microsoft says Internet-exposed Linux and Internet of Things (IoT) devices are being hijacked in brute-force attacks as part of a recently observed cryptojacking campaign.
After gaining access to a system, the attackers deploy a trojanized OpenSSH package that helps them backdoor the compromised devices and steal SSH credentials to maintain persistence.
"The patches install hooks that intercept the passwords and keys of the device's SSH connections, whether as a client or a server," Microsoft said.
"Moreover, the patches enable root login over SSH and conceal the intruder's presence by suppressing the logging of the threat actors' SSH sessions, which are distinguished by a special password."
The backdoor shell script deployed at the same time as the trojanized OpenSSH binary will add two public keys to the authorized_keys file for persistent SSH access.
It further allows the threat actors to harvest system information and install Reptile and Diamorphine open-source LKM rootkits to hide malicious activity on the hacked systems.
The threat actors also use the backdoor to eliminate other miners by adding new iptables rules and entries to /etc/hosts to drop traffic to hosts and IPs used by the operation's cryptojacking competitors.
"It also identifies miner processes and files by their names and either terminates them or blocks access to them, and removes SSH access configured in authorized_keys by other adversaries," Microsoft said.
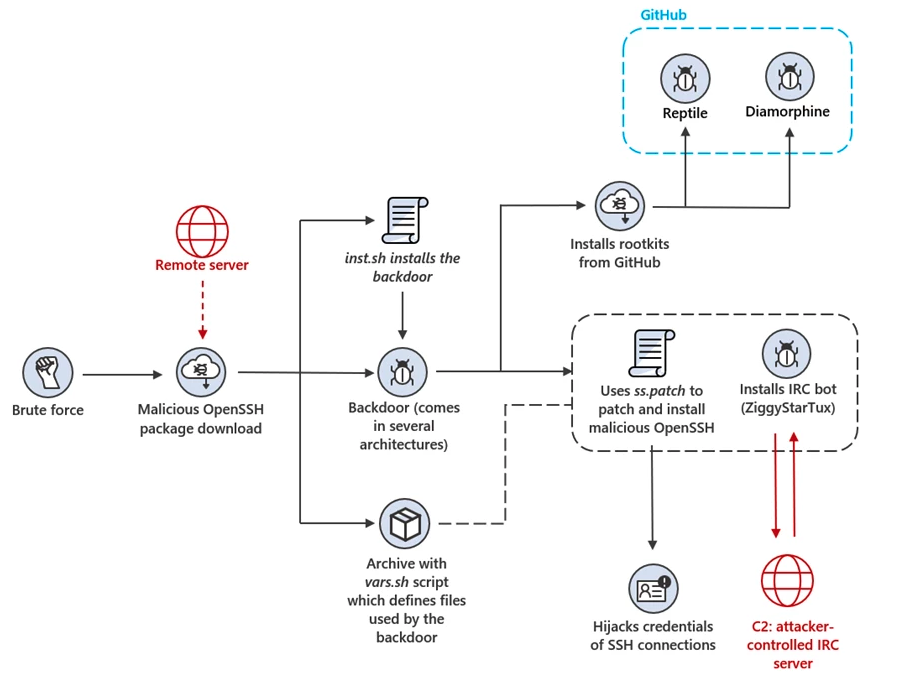
A version of the ZiggyStarTux open-source IRC bot also deployed in the attack comes with distributed denial of service (DDoS) capabilities and allows the operators to execute bash commands.
The backdoor malware utilizes multiple techniques to ensure its persistence on compromised systems, duplicating the binary across several disk locations and creating cron jobs to execute it periodically.
Additionally, it registers ZiggyStarTux as a systemd service, configuring the service file at /etc/systemd/system/network-check.service.
The C2 communication traffic between the ZiggyStarTux bots and the IRC servers is camouflaged using a subdomain belonging to a legitimate Southeast Asian financial institution hosted on the attacker's infrastructure.
While investigating the campaign, Microsoft saw the bots being instructed to download and execute additional shell scripts to brute-force every live host in the hacked device's subnet and backdoor any vulnerable systems using the trojanized OpenSSH package.
After moving move laterally within the victim's network, the attackers' end goal seems to be the installation of mining malware targeting Linux-based Hiveon OS systems designed for cryptomining.
"The modified version of OpenSSH mimics the appearance and behavior of a legitimate OpenSSH server and may thus pose a greater challenge for detection than other malicious files," Microsoft said.
"The patched OpenSSH could also enable the threat actors to access and compromise additional devices. This type of attack demonstrates the techniques and persistence of adversaries who seek to infiltrate and control exposed devices."


Comments
h_b_s - 10 months ago
So another attack that just exploits weak administrative practices to gain initial access. Maybe this wouldn't be as common if companies actually spent the money to hire people that knew what they were doing instead of burdening their Windows admins with the job or hiring people who's only qualification is that they think Linux is cool. I really wish there were a clearing house of information on who got pwned because of incompetent practices versus those that just got unlucky because they got hit with a genuine zero-day. It would be easier to know who to avoid doing business with.
crashulater - 10 months ago
This doesn't happen to real Unix/Linux men (m/f).
1. Don't have a ssh port open unless and when you need it.
2.. sshd doesn't need to run on port 22. Use an alternate port to confuse would be attackers.
3. Don't allow password login, allow only public key authentication
4. configure PermitRootLogin no
5. Since all public key logins are flawless, any login failure (detected real-time in your logs) is a reason to block the associated IP address at the firewall, e.g.: ipset add sshd_blocklist 2.92.0.0/14; which can interrupt a brute force attack inside of 1s.
6. Don't download software from any other place than your distribution's official site.
h_b_s - 10 months ago
No. 3 is arguable if staff use randomized characters for passcodes. It's convenient until staff lose their storage or laptop to hardware failure or it's stolen. No, encrypted drives aren't always foolproof. See the Bitlocker bug about trusting a drive's built in encryption.
No. 5 is not very useful in the real world. Attackers just rotate addresses. It may help, or it may hinder your own staff in diagnosing problems.
No. 6 is good when it's possible, but it's not always possible. That's the known weakness in Linux distros. Those repositories are only as secure as the people who administer them's diligence. Second, it's just not reasonable in the real world to ONLY install software from those repositories.
The real lesson here is to keep your credentials secure, whether you use passcodes or keys. The second lesson is even if you do everything right, someone, some where is going to find a way in. Don't store information in electronic form that would compromise the security of your employees or clients where it's externally reachable. And as consumers, don't volunteer information, and be skeptical of an organization's need-to-know claims.