
Microsoft has released security updates to address a Secure Boot zero-day vulnerability exploited by BlackLotus UEFI malware to infect fully patched Windows systems.
Secure Boot is a security feature that blocks bootloaders untrusted by the OEM on computers with Unified Extensible Firmware Interface (UEFI) firmware and a Trusted Platform Module (TPM) chip to prevent rootkits from loading during the startup process.
According to a Microsoft Security Response Center blog post, the security flaw (tracked as CVE-2023-24932) was used to bypass patches released for CVE-2022-21894, another Secure Boot bug abused in BlackLotus attacks last year.
"To protect against this attack, a fix for the Windows boot manager (CVE-2023-24932) is included in the May 9, 2023, security update release, but disabled by default and will not provide protections," the company said.
"This vulnerability allows an attacker to execute self-signed code at the Unified Extensible Firmware Interface (UEFI) level while Secure Boot is enabled.
"This is used by threat actors primarily as a persistence and defense evasion mechanism. Successful exploitation relies on the attacker having physical access or local admin privileges on the targeted device."
All Windows systems where Secure Boot protections are enabled are affected by this flaw, including on-premises, virtual machines, and cloud-based devices.
However, the CVE-2023-24932 security patches released today are only available for supported versions of Windows 10, Windows 11, and Windows Server.
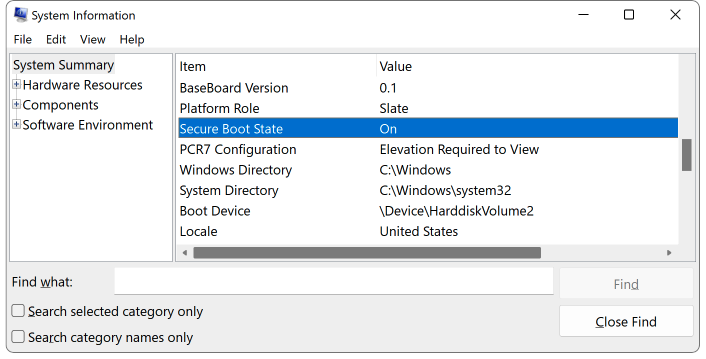
To determine if Secure Boot protections are enabled on your system, you can run the msinfo32 command from a Windows command prompt to open the System Information app.
Secure Boot is toggled on if you see a "Secure Boot State ON" message on the left side of the window after selecting "System Summary."
Manual steps required to mitigate CVE-2023-24932
While the security updates released today by Redmond contain a Windows boot manager fix, they are disabled by default and will not remove the attack vector exploited in BlackLotus attacks.
To defend their Windows devices, customers must undergo a procedure requiring multiple manual steps "to update bootable media and apply revocations before enabling this update."
To manually enable protections for the Secure Boot CVE-2023-24932 bypass bug, you have to go through the following steps in this exact order (otherwise, the system will no longer boot):
- INSTALL the May 9, 2023, updates on all affected systems.
- UPDATE your bootable media with Windows updates released on or after May 9, 2023. If you do not create your own media, you will need to get the updated official media from Microsoft or your device manufacturer (OEM).
- APPLY revocations to protect against the vulnerability in CVE-2023-24932.
Microsoft is also taking a phased approach to enforcing the protections addressing this security flaw to reduce customer impact due to enabling CVE-2023-24932 protections.
The rollout timeline includes three phases:
- May 9, 2023: The initial fix for CVE-2023-24932 is released. In this release, this fix requires the May 9, 2023, Windows Security Update and additional customer action to fully implement the protections.
- July 11, 2023: A second release will provide additional update options to simplify the deployment of the protections.
- First quarter 2024: This final release will enable the fix for CVE-2023-24932 by default and enforce bootmanager revocations on all Windows devices.
Microsoft also warned customers there is no way to revert the changes once CVE-2023-24932 mitigations are fully deployed.
"Once the mitigation for this issue is enabled on a device, meaning the revocations have been applied, it cannot be reverted if you continue to use Secure Boot on that device," Microsoft said.
"Even reformatting of the disk will not remove the revocations if they have already been applied."
Update: Revised title to explain that this is an optional fix.



Comments
Hemantunique - 11 months ago
So if we are using legacy bios mode and not using secure boot then we don’t have to worry about this vulnerability? Is this understanding correct?
serghei - 11 months ago
Correct, only systems with Secure Boot protections enabled are vulnerable.
hawk7000 - 11 months ago
But this is about a Secure Boot bypass vulnerability, right? Saying that "only systems with Secure Boot protections enabled are vulnerable" seems like a weird spin for a question about whether one should worry about a non-Secure Boot system.
It's rather than non-Secure Boot systems are *always* vulnerable to the type of mischief this vulnerability opens up for, as I understand it?
So, I suppose there is no need to be *more worried than usual*, but if it sounds concerning at all, maybe look into enabling Secure Boot.
NoneRain - 11 months ago
Attackers need local adm privileges, so, you would be already doomed.
There's no way in hell I'll apply the boot code integrity fix in my servers without extensive testing and reports from others. So, not going to patch it rn.
redwolfe_98 - 11 months ago
how can we know when the "boot media" from microsoft, for installing windows 10-22H2, has been updated to include the may 9th update?
lonegull - 11 months ago
I just tried getting this information from Microsoft support for Windows 11 and they don't seem to have any clue what I was talking about.
Astronomical - 11 months ago
Hi
FYI Microsoft’s Media Creation Tool (MCT) is now reported to be offering to create Windows ISO or USB Media for the latest Windows 10 Version 22H2 build 19045.2965 and Windows 11 Version 22H2 build 22621.1702.
Re : https://www.askwoody.com/forums/topic/its-may-updating-time/#post-2558067
plat1098 - 11 months ago
omg, this is a hot mess, I'm seriously debating whether to proceed...or not.
I don't think my threat model is to where some black hat would be interested. Trying to rationalize NOT applying this fix. It sounds kind of tricky and risky. Maybe I'll wait until there's a better fix.
redwolfe_98 - 11 months ago
here is another thread, saying that the ISO's from microsoft have been updated, and with information about how to check/verify the version/build that you have, after creating the install-media:
https://www.tenforums.com/windows-10-news/204684-additional-guidance-devices-using-secure-boot-cve-2023-24932-a.html
redwolfe_98 - 11 months ago
i followed the instructions to "apply the update," to enable the security-fix, and, no problems.
there is nothing really "tricky" about applying the security-fix-other than making sure that your "boot-media" is up-to-date, that it includes the may 9th windows update.
'just a few, simple commands, along with rebooting the computer, twice, to apply the security-fix.
stc169 - 11 months ago
If a vulnerability requires local admin access to exploit, is it really a vulnerability? Will a bad actor care about the vulnerability if they have administrative access to the system?
xxxnimdaworm - 11 months ago
I see that the following article is showing support for Windows Server 2012 Windows and Windows Server 2012 R2. Has anyone perform this procedure for Windows Server versions 2016, or 2019, and is it required for these versions of Server?
https://support.microsoft.com/en-us/topic/kb5025885-how-to-manage-the-windows-boot-manager-revocations-for-secure-boot-changes-associated-with-cve-2023-24932-41a975df-beb2-40c1-99a3-b3ff139f832d#takeaction5025885
INSTALL the May 9, 2023, updates on all supported versions and then restart the device before applying the revocations.
UPDATE your bootable media with Windows updates released on or after May 9, 2023. If you do not create your own media, you will need to get the updated official media from Microsoft or your device manufacturer (OEM).
APPLY revocations to protect against the vulnerability in CVE-2023-24932.
lonegull - 11 months ago
It can be reversed, but it requires deleting all the partitions Windows creates at install (EFI, NTFS C: and Recovery partitions). Then creating new partitions and reinstalling Windows. This deletes the EFI partition and the changes made with this update.