
As Lapsus$ data extortion gang announced that several of its members are taking a vacation, the City of London Police say they have arrested seven individuals connected to the gang.
A minor in Oxford, England, is believed to be among the leaders of the group that leaked closed source code and proprietary data from high-profile companies like Nvidia, Samsung, Microsoft, and Okta.
Lapsus$ has also claimed attacks on game developer Ubisoft, telecom company Vodafone, and e-commerce giant Mercado.
Some members may take a longer break
The latest public message from the group on Wednesday announced that some of its members were taking a vacation until March 30.
It is unclear how many members are in Lapsus$ but clues from their Telegram chats seem to suggest that there are members who speak English, Russian, Turkish, German, and Portuguese.
In a statement to the BBC, the City of London Police said that it had arrested seven people aged 16 to 21 “in connection with an investigation into a hacking group” and that all of them are under investigation.
No names have been released but the real identities of some Lapsus$ members have been known for a while as they had been doxed by rival hackers.
One of them is a teenager using the aliases White/Breachbase, a 17-year-old known from Oxford, England, who is believed to have accumulated over 300 BTC - around $13 million at today’s value, from hacking activities, SIM swapping being one of them.
Allegedly, White lost a good part of this fortune gambling and by leaving their system unprotected, allowing it to get hacked, twice.
The aliases above are just a few of more than a dozen the teenager used online, along with a couple of pseudonyms used on various platforms and hacker forums
Along with identifying information that included the real name, home address, date of birth, and education, rival hackers also published private photos of White with their family.
This was possible because of the long string of poor opsec decisions that left behind an identification trail, which appears to be a flaw that extends to other members of the Lapsus$ group as well.
A sample of this is exemplified by Bill Demirkapi, senior security engineer at Zoom, who noticed that Lapsus$ bragged about breaching Microsoft while stealing the source code:
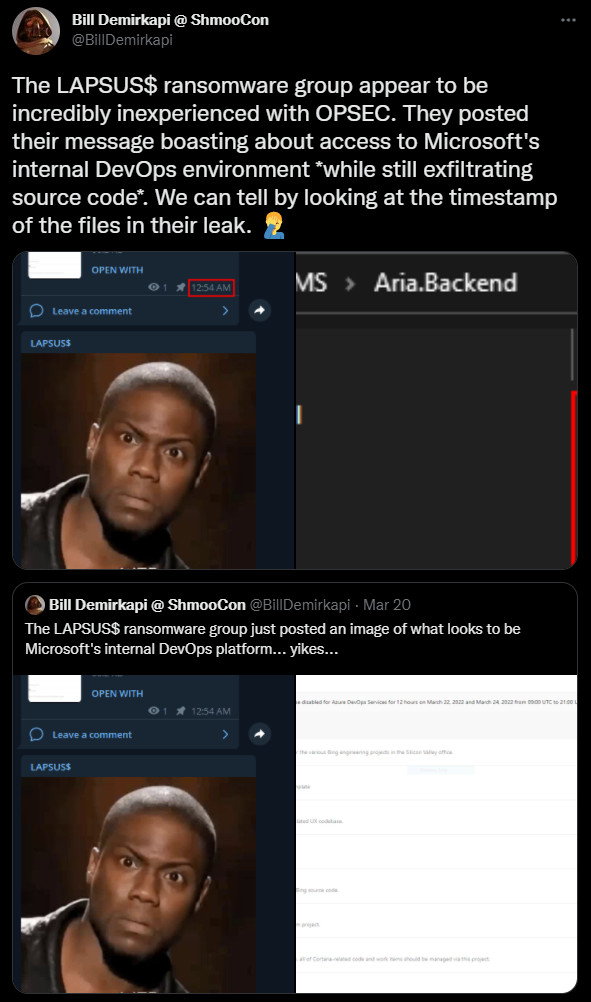
While this is not a crtitical mistake in revealing the identity of the group, it shows that their operational security skills are incredibly lacking, allowing security researchers and rivals alike to link email accounts and usernames to their real identity.
These operational security mistakes are likely what allowed law enforcement to identify and arrest many of the cybercrime gang's members.



Comments
GT500 - 2 years ago
Keep in mind that this is how much damage the groups who don't know what they are doing are capable of. Multiple gigabytes of source code and trade secrets from mega corporations like Microsoft and NVIDIA.
The guys who really know what they are doing? The guys you'll never hear about? The guys who are smart enough not to brag on social media about their hacking exploits? Imagine just how much damage they are capable of, and what they've already done behind the scenes.
yawnshard - 2 years ago
I hope his machine was not encrypted and they will find the others quickly. Skids being arrested is my eternal source of Schadenfreude. Also "taking a break"? Sounds like they are rattled and wiping the evidence.
They will not escape law enforcement! I hope the next few weeks they'll be looking over their shoulders and not sleep without trembling at the faintest knock on their doors.
NoneRain - 2 years ago
Any hacker arrest! It's always a pleasure to see scum being put down.
Amigo-A - 2 years ago
It seems strange that teenagers from the UK did this, and not military hackers from Russia.
Shauny67 - 2 years ago
"It seems strange that teenagers from the UK did this, and not military hackers from Russia."
Remember folks those of us that work in Cyber Security need to up our game as whilst they are driven by money - Just think if they had hacked Wall Street, Stock Exchanges etc. let alone Air Traffic Control
h_b_s - 2 years ago
"It seems strange that teenagers from the UK did this, and not military hackers from Russia."
Hardly. The demands Lapsus$ has publicly made pointed towards immaturity in the gang. Also, you're conveniently ignoring that the gang includes other nationalities. It's not "just UK teens". Learn to read. Most gangs like this involve multiple nationalities.
GT500 - 2 years ago
Was that a jab at the fact that hacking these days is often blamed on Russians with little to no real evidence?