
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added seven vulnerabilities to its list of actively exploited security issues, including those from Microsoft, Linux, and Jenkins.
The 'Known Exploited Vulnerabilities Catalog' is a list of vulnerabilities known to be actively exploited in cyberattacks and required to be patched by Federal Civilian Executive Branch (FCEB) agencies.
"Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the Known Exploited Vulnerabilities Catalog as a living list of known CVEs that carry significant risk to the federal enterprise," explains CISA.
"BOD 22-01 requires FCEB agencies to remediate identified vulnerabilities by the due date to protect FCEB networks against active threats. See the BOD 22-01 Fact Sheet for more information."
"The vulnerabilities listed in the catalog allow threat actors to perform a variety of attacks, including stealing credentials, gaining access to networks, remotely executing commands, downloading and executing malware, or stealing information from devices."
With the addition of these seven vulnerabilities, the catalog now contains 654 vulnerabilities, including the date that federal agencies must apply the associated patches and security updates.
The seven new vulnerabilities added this week are listed below, with CISA requiring all of them to be patched by May 16th, 2022.
| CVE Number | Vulnerability Title | Due Date |
|---|---|---|
| CVE-2022-29464 | WSO2 Multiple Products Unrestrictive Upload of File Vulnerability | 2022-05-16 |
| CVE-2022-26904 | Microsoft Windows User Profile Service Privilege Escalation Vulnerability | 2022-05-16 |
| CVE-2022-21919 | Microsoft Windows User Profile Service Privilege Escalation Vulnerability | 2022-05-16 |
| CVE-2022-0847 | Linux Kernel Privilege Escalation Vulnerability | 2022-05-16 |
| CVE-2021-41357 | Microsoft Win32k Privilege Escalation Vulnerability | 2022-05-16 |
| CVE-2021-40450 | Microsoft Win32k Privilege Escalation Vulnerability | 2022-05-16 |
| CVE-2019-1003029 | Jenkins Script Security Plugin Sandbox Bypass Vulnerability | 2022-05-16 |
How are these bugs used in attacks?
While it's helpful to know that a bug is exploited, it is even more helpful to understand how they are actively being used in attacks.
The WSO2 vulnerability tracked as CVE-2022-29464 was disclosed on April 18th, 2022, and a few days after, a public exploit was released. Rapid7 researchers soon saw the public PoC used in attacks to deploy web shells and coinminers.
The Windows 'User Profile Service Privilege Escalation' vulnerabilities tracked as CVE-2022-21919 and CVE-2022-26904 were both discovered by Abdelhamid Naceri and are subsequent bypasses of an original CVE-2021-34484 vulnerability fixed in August 2021. All of these vulnerabilities have had public PoC exploited disclosed, and BleepingComputer has been told that ransomware gangs use them to spread laterally through a Windows domain.
The Linux privilege escalation vulnerability known as 'DirtyPipe' is tracked as CVE-2022-0847 and was disclosed in March 2022. Soon after its disclosure, numerous proof-of-concept exploits were released, allowing users to gain root privileges quickly, as illustrated below.
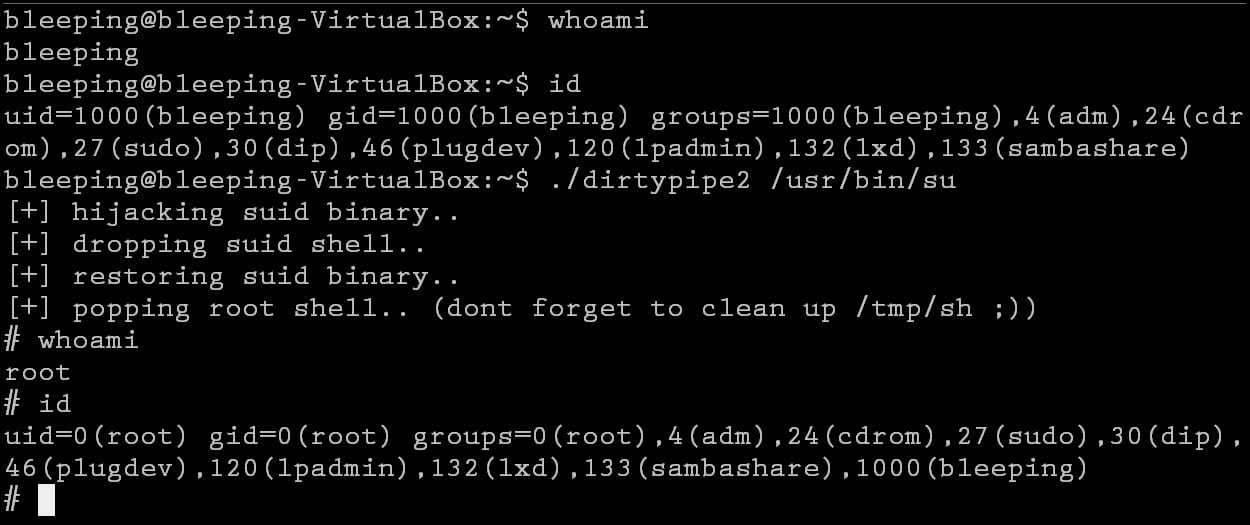
Source: BleepingComputer
The CVE-2021-40450 and CVE-2021-41357 'Microsoft Win32k Privilege Escalation' vulnerabilities were patched in October 2021 and are an interesting addition to the list, as there is no public mention of these being exploited in the wild.
Finally, the oldest vulnerability is the 'Jenkins Script Security Plugin Sandbox Bypass' bug tracked as CVE-2019-1003029, which has been used in the past by the Capoae Malware to deploy XMRig cryptominers.
It is strongly recommended that all security professionals and admins review the Known Exploited Vulnerabilities Catalog and patch any within their environment.



Comments
lonegull - 2 years ago
Need a whole Government Agency for something that can be done each month quite easily, in many cases automatically. Something that is a basic part of a systems administrator and system/network security.
Thought Linux was immune to security vulnerabilities and such problems were spotted before they ever got exploited (open-source code theory). All comments make you believe that it is O/S paradise, no errors ever happen and nobody ever gets hacked. *eye roll*