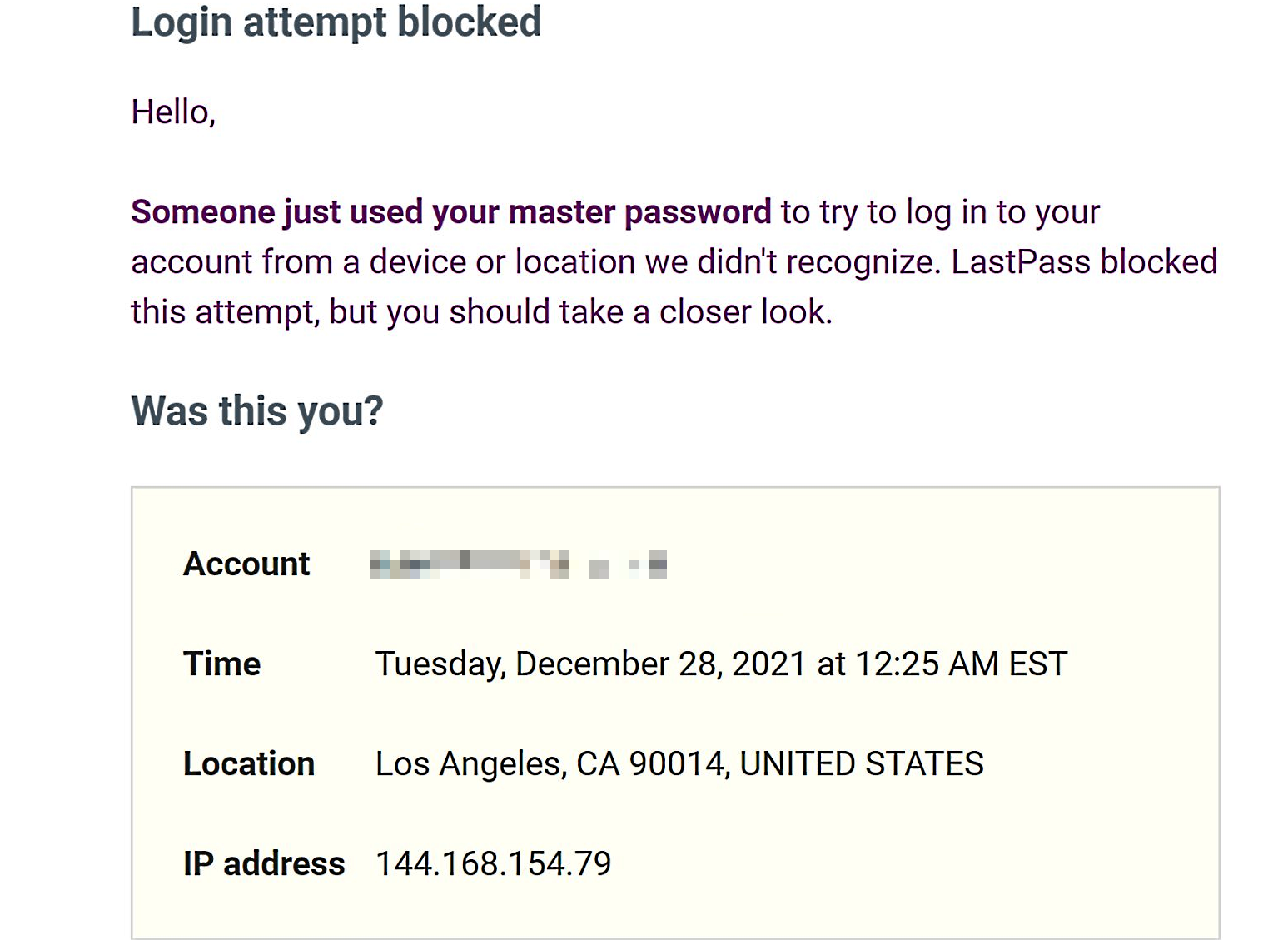
Many LastPass users report that their master passwords have been compromised after receiving email warnings that someone tried to use them to log into their accounts from unknown locations.
The email notifications also mention that the login attempts have been blocked because they were made from unfamiliar locations worldwide.
"Someone just used your master password to try to log in to your account from a device or location we didn't recognize," the login alerts warn.
"LastPass blocked this attempt, but you should take a closer look. Was this you?"
Reports of compromised LastPass master passwords are streaming in via multiple social media sites and online platforms, including Twitter, Reddit, and Hacker News (original report from Greg Sadetsky).
LastPass says it's credential stuffing
LogMeIn Global PR/AR Senior Director Nikolett Bacso-Albaum told BleepingComputer that "LastPass investigated recent reports of blocked login attempts and determined the activity is related to fairly common bot-related activity, in which a malicious or bad actor attempts to access user accounts (in this case, LastPass) using email addresses and passwords obtained from third-party breaches related to other unaffiliated services."
"It’s important to note that we do not have any indication that accounts were successfully accessed or that the LastPass service was otherwise compromised by an unauthorized party. We regularly monitor for this type of activity and will continue to take steps designed to ensure that LastPass, its users, and their data remain protected and secure," Bacso-Albaum added.
However, users receiving these warnings have stated that their passwords are unique to LastPass and not used elsewhere. BleepingComputer has asked LastPass about these concerns but has not received a reply as of yet.
While LastPass didn't share any details regarding how the threat actors behind these credential stuffing attempts, security researchers Bob Diachenko said he recently found thousands of LastPass credentials while going through Redline Stealer malware logs.
BleepingComputer was also told by LastPass customers who received such login alerts that their emails were not in the list of login pairs harvested by RedLine Stealer found by Diachenko.
OK, I received a few requests to check emails in the redline stealer logs, and there was none in the records. So apparently this was not the source of the attack (unfortunately - since it would make it easier to understand the vector).
— Bob Diachenko (@MayhemDayOne) December 28, 2021
This means that, at least in the case of some of these reports, the threat actors behind the takeover attempts used some other means to steal their targets' master passwords.
Some customers have also reported changing their master passwords since they received the login warning, only to receive another alert after the password was changed.
To make things even worse, customers who tried disabling and deleting their LastPass accounts after receiving these warnings also report [1, 2] receiving "Something went wrong: A" errors after clicking the "Delete" button.
Someone tried my @LastPass master password earlier yesterday and then someone just tried it again a few hours ago after I changed it. What the hell is going on?
— Valcrist (@Valcristerra) December 28, 2021
LastPass users are advised to enable multifactor authentication to protect their accounts even if their master password was compromised.
Two years ago, in September 2019, LastPass fixed a security vulnerability in the password manager's Chrome extension that could have allowed threat actors to steal the credentials last used for logging into a site.
Update December 28, 12:36 EST: Added LastPass statement.
Update December 28, 15:08 EST: Added info on LastPass login pairs stolen by RedLine Stealer malware.
Update December 29, 03:37 EST: In an update to the original statement, LastPass VP of Product Management Dan DeMichele told BleepingComputer that some of the login warnings were likely sent in error.
As previously stated, LastPass is aware of and has been investigating recent reports of users receiving e-mails alerting them to blocked login attempts.
We quickly worked to investigate this activity and at this time we have no indication that any LastPass accounts were compromised by an unauthorized third-party as a result of this credential stuffing, nor have we found any indication that user’s LastPass credentials were harvested by malware, rogue browser extensions or phishing campaigns.
However, out of an abundance of caution, we continued to investigate in an effort to determine what was causing the automated security alert e-mails to be triggered from our systems.
Our investigation has since found that some of these security alerts, which were sent to a limited subset of LastPass users, were likely triggered in error. As a result, we have adjusted our security alert systems and this issue has since been resolved.
These alerts were triggered due to LastPass’s ongoing efforts to defend its customers from bad actors and credential stuffing attempts. It is also important to reiterate that LastPass’ zero-knowledge security model means that at no time does LastPass store, have knowledge of, or have access to a users’ Master Password(s).
We will continue to regularly monitor for unusual or malicious activity and will, as necessary, continue to take steps designed to ensure that LastPass, its users and their data remain protected and secure.



Comments
Izzyoraintee - 2 years ago
If you changed your master password and it gets tried a few minutes later you might have a keylogger. Change the password from another device and pave your PC.
Also, "LastPass users are advised to enable multifactor authentication to protect their accounts even if their master password was compromised." That should be "...even if their master password WASN'T compromised." (of course you should if it WAS!)
plaasjaapie - 2 years ago
I expect that most of these problems that lastPass, which I use, sees are occurring with users using VPN services with server options outside the US, which I regular employ with my VPN. I've had this problem with lastPass. It goes away as soon as you reset your VPN to a local server.
Phil8192 - 2 years ago
"I expect that most of these problems that lastPass, which I use, sees are occurring with users using VPN services with server options outside the US, which I regular employ with my VPN. I've had this problem with lastPass. It goes away as soon as you reset your VPN to a local server. "
You are probably correct. Even without using TOR or a VPN, Google has had this nasty feature for a number of years wherein it sends dire-sounding warning messages if one should log into one's account from a friend's computer or the IP address changes, as the IP lease regularly expires and the ISP assigns a new IP address to one's modem. A few years ago Google even locked me out of several email accounts for one to two weeks, because I wasn't aware of my IP address having changed and didn't respond to the warning email messages fast enough. For people using VPNs or traveling and logging in from various locations around the country or around the world it would be good if outfits like LastPass and Google would provide a way for us to disable this paranoia feature, but they don't
plaasjaapie - 2 years ago
It's not that hard now. If you run into the problem while traveling, just use your VPN to access a server close to the place where you live and work. You can use the same dodge with streaming services as well.
force41 - 2 years ago
Credential stuffing? Sounds more like a lack of transparency from LogMeIn.
I don't believe LastPass has the same level of professional security since it was sold. Thankfully, there are alternatives, particularly non-cloud ones.
plaasjaapie - 2 years ago
Sold?
Wannabetech1 - 1 year ago
Yes, Joe Siegrist, a co-founder and the man behind the tech, sold it a few years ago.
dashrender - 2 years ago
So much for them fixing the false emails. I got one at 3:32 PM CST
Forevermaat - 2 years ago
So the emails were false alerts? No passwords were compromised (from LassPass's end).
avalanchio - 2 years ago
Yes, password protection is a very important factor when it comes to data privacy....