
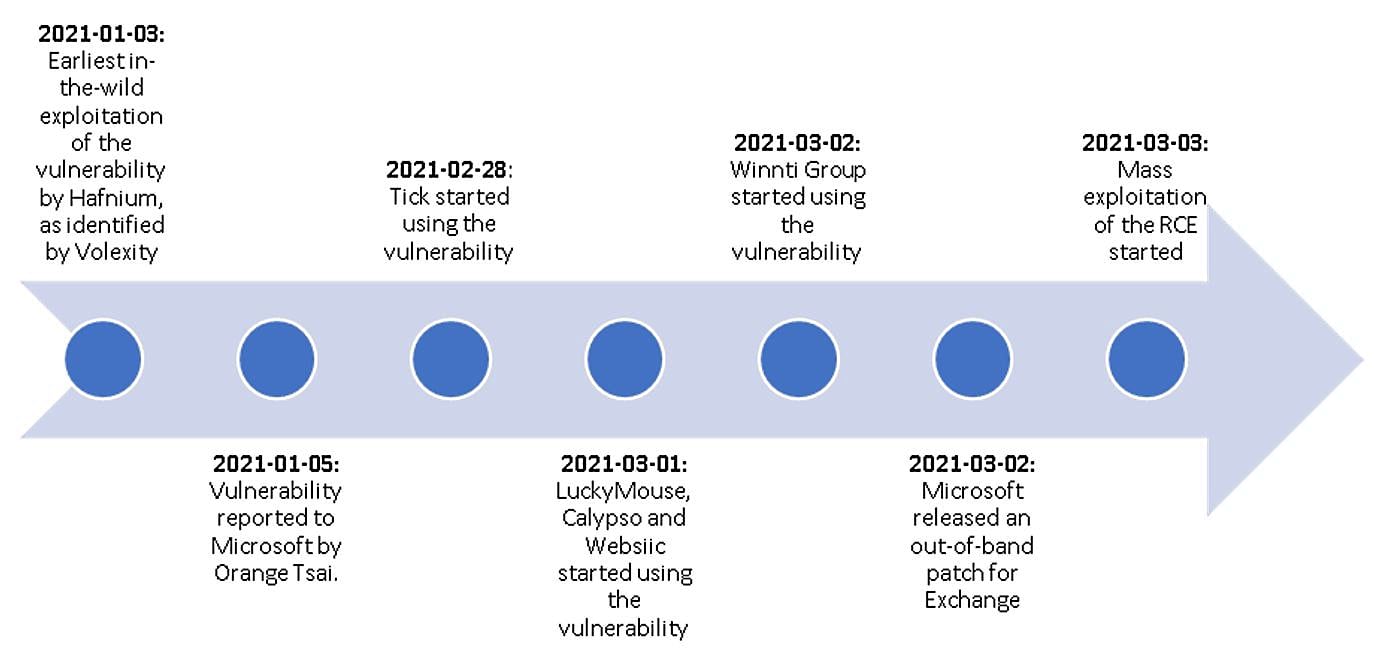
More state-sponsored hacking groups have joined the ongoing attacks targeting tens of thousands of on-premises Exchange servers impacted by severe vulnerabilities tracked as ProxyLogon.
After Microsoft's initial report that the vulnerabilities were actively exploited by a Chinese APT group named Hafnium, Slovak internet security firm ESET shared info on at least three other Chinese-backed hacking groups abusing the ProxyLogon flaws in ongoing attacks.
Besides those three (APT27, Bronze Butler aka Tick, and Calypso), ESET also said that it also identified several "additional yet-unclassified clusters."
In a Friday update to their announcement, Microsoft said that several other threat actors "beyond HAFNIUM" are also exploiting the four critical Exchange flaws.
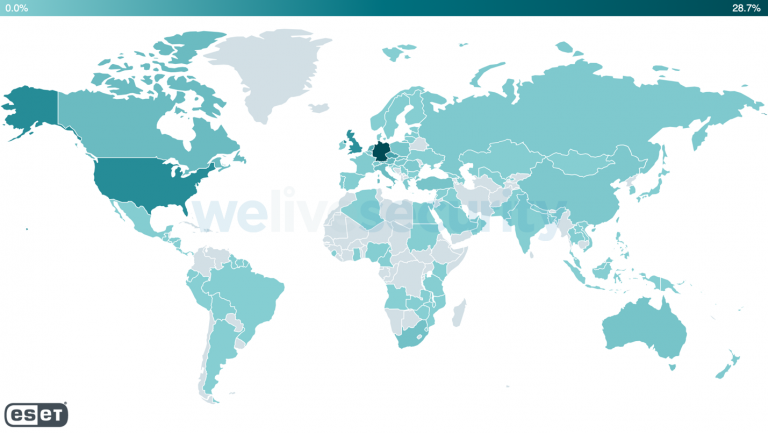
Based on ESET's (incomplete) telemetry, web shells have already been deployed on over 5,000 unique Exchange servers from over 115 countries.
Exchange servers attacked by multiple hacking groups
ESET has now published a new report saying that unpatched Exchange servers are currently hunted down by "at least 10 APT groups."
On top of the previously mentioned APTs (APT27, Tick, and Calypso), ESET's new list also includes Winnti Group, Tonto Team, Mikroceen, and a newly detected threat actor dubbed Websiic.
While analyzing telemetry data, the company has also spotted ShadowPad, "Opera" Cobalt Strike, IIS backdoor, and DLTMiner activity by unknown APT groups.
ESET also provided a short rundown of these threat groups and behavior clusters' malicious activity:
- Tick (Bronze Butler) – compromised the webserver of a company based in East Asia that provides IT services. As in the case of LuckyMouse and Calypso, the group likely had access to an exploit prior to the release of the patches.
- LuckyMouse (APT27) – compromised the email server of a governmental entity in the Middle East. This APT group likely had an exploit at least one day before the patches were released, when it was still a zero-day.
- Calypso – compromised the email servers of governmental entities in the Middle East and in South America. The group likely had access to the exploit as a zero-day. In the following days, Calypso operators targeted additional servers of governmental entities and private companies in Africa, Asia, and Europe.
- Websiic – targeted seven email servers belonging to private companies (in the domains of IT, telecommunications, and engineering) in Asia and a governmental body in Eastern Europe.
- Winnti Group – compromised the email servers of an oil company and a construction equipment company in Asia. The group likely had access to an exploit prior to the release of the patches.
- Tonto Team – compromised the email servers of a procurement company and of a consulting company specialized in software development and cybersecurity, both based in Eastern Europe.
- ShadowPad activity – compromised the email servers of a software development company based in Asia and a real estate company based in the Middle East. ESET detected a variant of the ShadowPad backdoor dropped by an unknown group.
- The “Opera” Cobalt Strike – targeted around 650 servers, mostly in the US, Germany, the UK, and other European countries just a few hours after the patches were released.
- IIS backdoors – ESET observed IIS backdoors installed via web shells used in these compromises on four email servers located in Asia and South America. One of the backdoors is publicly known as Owlproxy.
- Mikroceen – compromised the exchange server of a utility company in Central Asia, which is the region this group typically targets.
- DLTMiner – ESET detected the deployment of PowerShell downloaders on multiple email servers that were previously targeted using the Exchange vulnerabilities. The network infrastructure used in this attack is linked to a previously reported coin-mining campaign.
"It is now clearly beyond prime time to patch all Exchange servers as soon as possible," ESET concluded.
"Even those not directly exposed to the internet should be patched because an attacker with low, or unprivileged, access to your LAN can trivially exploit these vulnerabilities to raise their privileges while compromising an internal (and probably more sensitive) Exchange server, and then move laterally from it."
Detailed info on the servers compromised by these hacking groups and the threat actors behind the not yet attributed malicious activity, including indicators of compromise, can be found in ESET's report.
Over 46,000 servers still exposed to attacks
After scanning 250,000 Exchange servers worldwide, the Dutch Institute for Vulnerability Disclosure (DIVD) reported Tuesday that it found 46,000 servers unpatched against the heavily exploited ProxyLogon vulnerabilities.
The critical vulnerabilities were patched by Microsoft on March 2nd, with additional security updates issued by the company this week for multiple unsupported Exchange versions.
Redmond has also updated the Microsoft Safety Scanner (MSERT) tool to help customers detect web shells deployed in the ongoing Exchange Server attacks.
You can find additional info on installing the security updates in this article published by the Microsoft Exchange Team.
If you haven't yet patched and detect signs of compromise, you have to remove the web shells deployed by the attackers, change all credentials, and investigate additional malicious activity on your servers.



Comments
Technika999 - 3 years ago
On a side note, Microsoft should've extended the Windows 7 End of Life support instead of bringing updates to a halt in January 2020 during a Pandemic when many users who are working remotely from home using their own personal computers. And considering that Windows 7 still holding a significant share of the windows market is just asking for trouble for companies who have to allow these remote workers on their networks. At the end of the day Microsoft still supports windows 7 updates but just only machines running in enterprises or corporate licensed environments. This should still be opened to all general users who have not gotten the chance to upgrade to windows 10 for whatever reason. I think they still can change it and reverse the decision to open the updates back up until the pandemic is over or we will have a lot more casualties from these breaches. I don't use windows 7 personally but I know many who still use it on their home personal PC's and remote in to their office networks.
We can't force remote workers to upgrade their PC's to Windows 10 considering some prohibiting factors for the user like the spending money now in these hard times for purchasing a new computer or hardware upgrades if the current home PC is not capable of running windows 10 at an acceptable performance.
Concerned SysAdmin
TsVk! - 3 years ago
People were given 3 years extended security updates and still now access to some critical patches. How much time is enough? If after years of being warned that something is going to happen, then it does, I don't really feel any sympathy for the people who are "suddenly stuck". One literally has to be using a 6+ year old machine to not be able to legally update to hardware and security supported 8 or 10 now.
Corporate machines running 7 are modern machines but have specialised software, which is why they continue to use 7. They also have enterprise security on a networking level and pay $$$'s for the support. It is not the same.
As a sysadmin I'm more surprised that your only gripe is the pitiful woes of home users and not the major concern of Exchange being busted wide open and the effect on email security globally. Even if your server didn't get owned (if you use Exchange, which I don't) it will still effect trust between companies and governments and increase incidence of malicious mail and conversation intercepts.