Emotet, one of the most dangerous email spam botnets in recent history, is being uninstalled today from all infected devices with the help of a malware module delivered in January by law enforcement.
The botnet's takedown is the result of an international law enforcement action that allowed investigators to take control of the Emotet's servers and disrupt the malware's operation.
Emotet was used by the TA542 threat group (aka Mummy Spider) to deploy second-stage malware payloads, including QBot and Trickbot, onto its victims' compromised computers.
TA542's attacks usually led to full network compromise and the deployment of ransomware payloads on all infected systems, including ProLock or Egregor by Qbot, and Ryuk and Conti by TrickBot.
How the Emotet uninstaller works
After the takedown operation, law enforcement pushed a new configuration to active Emotet infections so that the malware would begin to use command and control servers controlled by the Bundeskriminalamt, Germany's federal police agency.
Law enforcement then distributed a new Emotet module in the form of a 32-bit EmotetLoader.dll to all infected systems that will automatically uninstall the malware on April 25th, 2021.
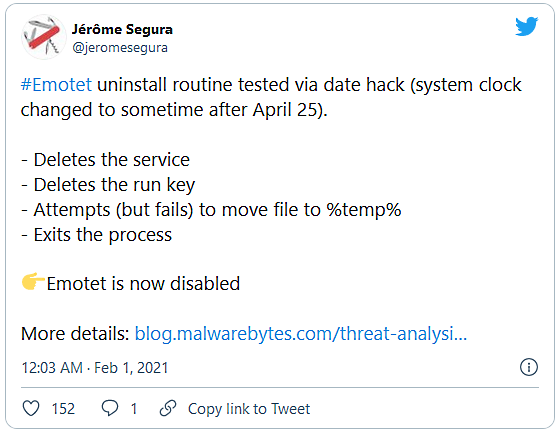
Malwarebytes security researchers Jérôme Segura and Hasherezade took a closer look at the uninstaller module delivered by law enforcement-controlled to Emotet servers.
After changing the system clock on a test machine to trigger the module, they found that it only deletes associated Windows services, autorun Registry keys, and then exits the process, leaving everything else on the compromised devices untouched.
"For this type of approach to be successful over time, it will be important to have as many eyes as possible on these updates and, if possible, the law enforcement agencies involved should release these updates to the open internet so analysts can make sure nothing unwanted is being slipped in," Marcin Kleczynski, CEO of Malwarebytes, told BleepingComputer.
"That all said, we view this specific instance as a unique situation and encourage our industry partners to view this as an isolated event that required a special solution and not as an opportunity to set policy moving forward."
German federal police agency behind Emotet uninstaller module
In January, when law enforcement took down Emotet, BleepingComputer was told by Europol that the German Bundeskriminalamt (BKA) federal police agency was responsible for creating and pushing the uninstall module.
"Within the framework of the criminal procedural measures carried out at international level, the Bundeskriminalamt has arranged for the malware Emotet to be quarantined in the computer systems affected," Bundeskriminalamt told Bleepingcomputer.
In a January 28th press release, the US Department of Justice (DOJ) also confirmed that the Bundeskriminalamt pushed the uninstaller module to Emotet-infected computers.
"Foreign law enforcement, working in collaboration with the FBI, replaced Emotet malware on servers located in their jurisdiction with a file created by law enforcement," the DOJ said.
"The law enforcement file does not remediate other malware that was already installed on the infected computer through Emotet; instead, it is designed to prevent additional malware from being installed on the infected computer by untethering the victim computer from the botnet."
Emotet removal delayed for collecting more evidence
BleepingComputer was told in January by the Bundeskriminalamt that the delay in uninstalling was for seizing evidence and clean the machines of the malware.
An identification of the systems affected is necessary in order to seize evidence and to enable the users concerned to carry out a complete system clean-up to prevent further offences. For this purpose, the communication parameters of the software have been adjusted in a way that the victim systems no longer communicate with the infrastructure of the offenders but with an infrastructure created for the seizure of evidence. -- Bundeskriminalamt
"Please understand that we cannot provide any further information as the investigations are still ongoing," the Bundeskriminalamt told BleepingComputer when asked for more info.
When BleepingComputer reached out again for comment about today's operation, we did not receive a response.
The FBI also declined to comment when asked this week if the Emotet removal operation from devices located in the USA is still planned to occur on Sunday, April 25th.
Earlier this month, FBI coordinated a court-approved operation to remove web shells from US-based Microsoft Exchange servers compromised using ProxyLogon exploits without first notifying the servers' owners.
The FBI said that it only removed web shells and did not apply security updates or removed other malware that threat actors may have deployed on the servers.



Comments
Some-Other-Guy - 3 years ago
The problem is that the owners of infected computers are not told of the infections, are not told of the changes made to their systems by German Police (or FBI in the earlier case) and are not told that evidence was being collected from their computers
Many of these systems are still infected and will remain infected until the owners are notified
and that will be..........when? exactly?
I don't necessarily have a problem with forcibly removing malware in a case such as this as long as the computers owner is immediately notified of the malware removal, what information is being collected and by whom, the purpose of it's collection, who it will be shared with, and how it will be used by the German Police, the FBI or anyone else who will have access to it
As it stands, the German Police now have a botnet of their own
Does anyone else see a problem here?
yawnshard - 3 years ago
CERT or BSI do that, or the respective CERT of that country.
Who cares when and if they are notified?
If they run a company with sysadmins this incompetent not to listen to their national CERT?
So many logical fallacies, no the Germans run NO botnet. The reason why they waited so long was to give terrible sysadmins time IF they were infected. That was months ago now.
Do I see a problem? Yeah, a lot of admins are not doing their job. Not reading CERT bulletins, not securing their net. Not checking their systems with YARA rules?
Save us the hyperbole.
Some-Other-Guy - 3 years ago
You are trying to justify criminal behavior by the Police
They have no authority to unilaterally make arbitrary changes to ANY computer that does not belong to them
The Police do not have that authority and the FBI do not have that authority
If you believe that they do, then "WE ALL" have the authority to make arbitrary changes to "YOUR" computers without your permission or notification, and we grant ourselves the authority to wipe / encrypt or change your data at our discretion
(It's for your own good - and for the protection of personal data)
If we do not "knowingly" grant you the authority (without coercion or one sided agreements), you do not have the authority
"Your" Laws do not apply here!
AlfaX - 3 years ago
"You are trying to justify criminal behavior by the Police
They have no authority to unilaterally make arbitrary changes to ANY computer that does not belong to them
The Police do not have that authority and the FBI do not have that authority
If you believe that they do, then "WE ALL" have the authority to make arbitrary changes to "YOUR" computers without your permission or notification, and we grant ourselves the authority to wipe / encrypt or change your data at our discretion
(It's for your own good - and for the protection of personal data)
If we do not "knowingly" grant you the authority (without coercion or one sided agreements), you do not have the authority
"Your" Laws do not apply here!"
As emotet is one of the nastiest variants out there, I welcome this. I spent months trying to clean a corporate network of emotet. In the end, we had to take the the entire company offline, manually pull ethernet from systems, and clean them one by one thanks to Emotet's worm abilities. If someone had given me the option of utilizing this "kill switch", I would have paid untold amounts of money.
You seem to forget that the "hacking" laws that apply to you and I do not apply to government agencies when they're trying to remove a near unstoppable infection from over 1.6 million machines globally.
Not sure why you're so up in arms over this.
Some-Other-Guy - 3 years ago
You and I both are not sure why I am up in arms over this
I read the story wrong and that has been happening far too often lately
It's time for me to take a break
Sorry for the trouble
yawnshard - 3 years ago
@Some-Other-Guy:
Just because you emotionally FEEL that way doesn't imply correctness. But having pointed out these logical fallacies, there is no grounds for serious discussions. Which is why I will allocate my free time with more meaningful tasks than reacting to this bait.
As other people already pointed out the government has the legal grounds for their own actions. Should you like it or not. Good day sir.
EmanuelJacobsson - 3 years ago
Dont feed the troll.
NoneRain - 3 years ago
He is a troll... better just ignore him. You can't argue vs non-sense.
No1gr8 - 3 years ago
"systems no longer communicate with the infrastructure of the offenders but with an infrastructure created for the seizure of evidence." This malware gave the hackers full control of a system. I wonder how BKA and the FBI collected this evidence for six months and maybe what collateral information was obtained.
It's a new world out there. I hear people all the time say I have nothing to hide, so I don't care what they see. What if you have some emails where you and a friend were being critical of an administration, raising concerns of vaccines or secure voting? It's not new to see people losing jobs and family over these topics.
Wolverine 7 - 3 years ago
Yes it comes down to the basic integrity and trancparency of the agencies involved,..so obviously we have notthing to worry about,..(exept for the fact their mostly headed up by powermongering fruitcakes),..
The internet is getting like the new wild west out there...
Some-Other-Guy - 3 years ago
OK, got it now
Read it wrong!
They are not collecting evidence from infected computers as of right now
They were collecting evidence until now
So, the German Police did not make this into their own private botnet
Note to self:
Calm the Bleep down and take a deep breath