Millions of email addresses collected by Emotet botnet for malware distribution campaigns have been shared by the Federal Bureau of Investigation (FBI) as part of the agency’s effort to clean infected computers.
Individuals and domain owners can now learn if Emotet impacted their accounts by searching the database with email addresses stolen by the malware.
Over 4 million emails collected
Earlier this year, law enforcement took control of Emotet botnet’s infrastructure that involved several hundreds of servers all over the world.
Using the communication line to infected computers, law enforcement on April 25 was able to send out an update that uninstalled Emotet malware on all affected systems.
Apart from computer systems, Emotet also compromised a large number of email addresses and used them for its operations. The FBI now wants to give the owners of these email addresses a quick way to check if they’ve been affected by Emotet.
For this purpose, the agency and the Dutch National High Technical Crimes Unit (NHTCU) shared 4,324,770 email addresses that had been stolen by Emotet with the Have I Been Pwned (HIBP) data breach notification service.
Troy Hunt, the creator of the HIBP service says that 39% of these email addresses had already been indexed as part of other data breach incidents.
The email addresses belong to users from multiple countries. They came from logins stored on Emotet’s infrastructure for sending out malicious emails or had been harvested from the users’ web browsers.
Given its sensitive nature, the Emotet data is not publicly searchable. Subscribers to the service that were impacted by the Emotet breach have already been alerted, says HIBP creator, Troy Hunt.
Referring to the verification process, Hunt says that “individuals will either need to verify control of the address via the notification service or perform a domain search to see if they're impacted.”
The Dutch National Police, which was part of the Emotet takedown operation, has a similar lookup service, where users can check if Emotet compromised their emails.
Individuals can type in an email address, and if the account is part of the seized data from the Emotet botnet, the Dutch police will send it a message with instructions on what to do next. On February 3rd, the Dutch police added 3.6 million email addresses to its checking service.
Another service, called Have I Been Emotet from cybersecurity company TG Soft launched on October 1, 2020. It checks if Emotet used an email address as a sender or a recipient. However, it was last updated on January 25th, two days before the botnet was taken down.
Huge takedown effort
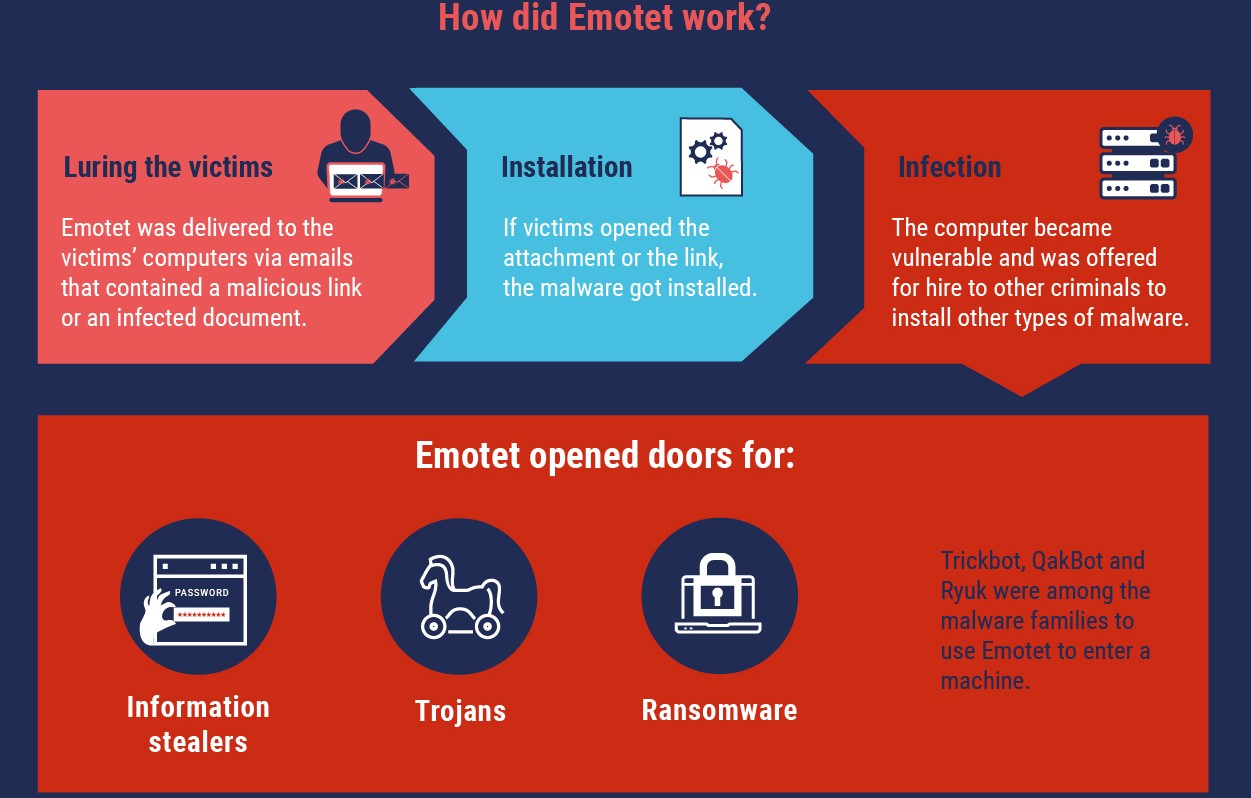
Emotet is among this decade’s most prominent botnets causing hundreds of millions of dollars in damage across the world and infecting around 1.6 million computers in about nine months.
It played a key role in the distribution chain for several ransomware strains as it often delivered QakBot and Trickbot malware on the compromised network, which further dropped ProLock or Egregor, and Ryuk and Conti, respectively.
On January 27th, all three Epochs - subgroups of the botnet with a separate infrastructure - of Emotet fell under the control of law enforcement agencies. The operation was possible with the effort from authorities in the Netherlands, Germany, the United States, the United Kingdom, France, Lithuania, Canada, and Ukraine.




Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now