Comcast Cable Communications, doing business as Xfinity, disclosed on Monday that attackers who breached one of its Citrix servers in October also stole customer-sensitive information from its systems.
On October 25, roughly two weeks after Citrix released security updates to address a critical vulnerability now known as Citrix Bleed and tracked as CVE-2023-4966, the telecommunications company found evidence of malicious activity on its network between October 16 and October 19.
Cybersecurity company Mandiant says the Citrix flaw had been actively exploited as a zero-day since at least late August 2023.
Following an investigation into the impact of the incident, Xfinity discovered on November 16 that the attackers also exfiltrated data from its systems, with the data breach affecting 35,879,455 people.
"After additional review of the affected systems and data, Xfinity concluded on December 6, 2023, that the customer information in scope included usernames and hashed passwords," the company said.
"[F]or some customers, other information may also have been included, such as names, contact information, last four digits of social security numbers, dates of birth and/or secret questions and answers. However, the data analysis is continuing."
Users' passwords reset without any info
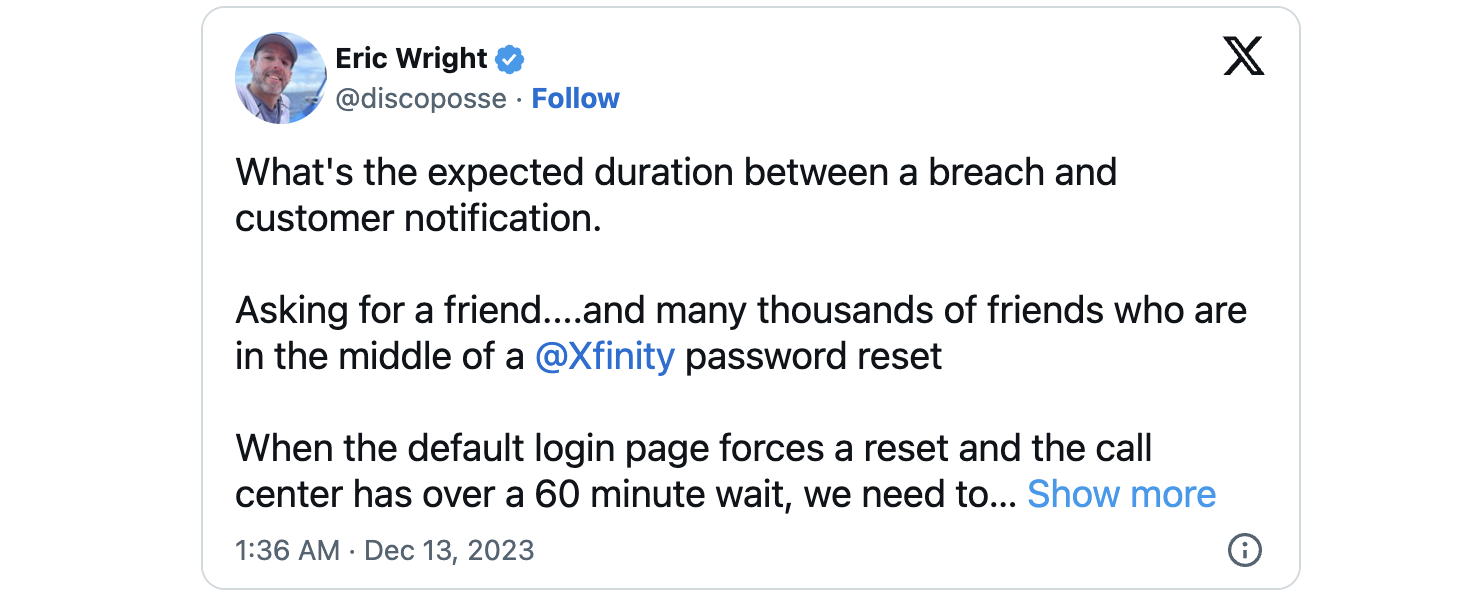
While Xfinity says it has asked users to reset their passwords to protect affected accounts, customers report that they had been getting password reset requests last week without any indication as to why that was happening.
"To protect your account, we have proactively asked you to reset your password. The next time you login to your Xfinity account, you will be prompted to change your password, if you haven't been asked to do so already," the company says in a data breach notice published on its website.
One year ago, Xfinity customers also had their accounts hacked in widespread credential stuffing attacks bypassing two-factor authentication.
Compromised accounts were then used to reset account passwords for other services, including the Coinbase and Gemini crypto exchanges.
Update December 18, 19:08 EST: A Comcast spokesperson shared the following statement with BleepingComputer after the article was published but didn't share more details on the number of individuals affected by the data breach. The company added that its operations were not impacted and that it received no ransom demand after the incident.
We are providing notice to customers about a data security incident which exploited a vulnerability previously announced by Citrix, a software provider used by Xfinity and thousands of other companies worldwide. We promptly patched and mitigated the vulnerability. We are not aware of any customer data being leaked anywhere, nor of any attacks on our customers.
In addition, we required our customers to reset their passwords and we strongly recommend that they enable two-factor or multi-factor authentication, as many Xfinity customers already do. We take the responsibility to protect our customers very seriously and have our cybersecurity team monitoring 24x7.
Update December 19, 05:40 EST: Added info on the number of people affected by the data breach.



Comments
gryphenwings - 5 months ago
They all say "we take data security very seriuosly". When does this ever end? At this point you might as well just publish all your information online and let the criminals have at it.
fjc11 - 5 months ago
I agree. Also claiming to monitor systems 24x7, but miss the exfiltration of data belonging to 35,879,455 people from its systems. How does that amount of data slip through unnoticed?
tmcsters - 5 months ago
It ends when companies start taking security seriously, and fund IT security departments appropriately. Large businesses that depend upon IT systems need to at minimum invest 3% of revenue into security. These events will continue to happen to orgs that won't invest in security.
Whaduu - 5 months ago
It ends when significant fines get levied and enforced. Fighting cybercrime should be a national imperative because it is becoming a serious threat to our way of life and the economic continuity of the country. For companies that don't loose all their customers after a breach, the only pain that will work is loss of $$ through fines or class-action suits (that are quickly adjudicated and enforced).
Cauthon - 5 months ago
Many sites demand that we use passwords with a certain minimum length, upper and lower case, numbers and special characters - clearly intending to defend against brute force intrusions. Malware can search through huge amounts of data per second. How is that possible when it takes more than a second to log in to a web site with the correct password? Doesn't that provide a lot of protection, even without 2-factor authentication?
Hmm888 - 5 months ago
These breaches occur at the backend, not our own devices unless you're careless or ignorant.
The fact is everything businesses say regarding privacy and security is nothing more than optics. They tell people, especially the naïve and gullible what they want to hear.
The issue is becoming worse and ubiquitous thanks to lazy and overworked IT Admins and their section heads. As long as these companies have ransomware insurance they will do very little to be proactive. There needs to be a legislative ban on this kind of insurance and laws changed so CEOs and others receive jail time and criminal records for their incompetence and ineptitude.
static_nuance - 1 month ago
Unfortunately it appears hackers still have access into Comcast’s systems. Users are getting their accounts hacked again similar to the account stuffing issue from about a year ago.