
Microsoft has released the KB5004945 emergency security update to fix the actively exploited PrintNightmare zero-day vulnerability in the Windows Print Spooler service impacting all Windows versions. However, the patch is incomplete and the vulnerability can still be locally exploited to gain SYSTEM privileges.
The remote code execution bug (tracked as CVE-2021-34527) allows attackers to take over affected servers via remote code execution (RCE) with SYSTEM privileges, as it will enable them to install programs, view, change, or delete data, and create new accounts with full user rights.
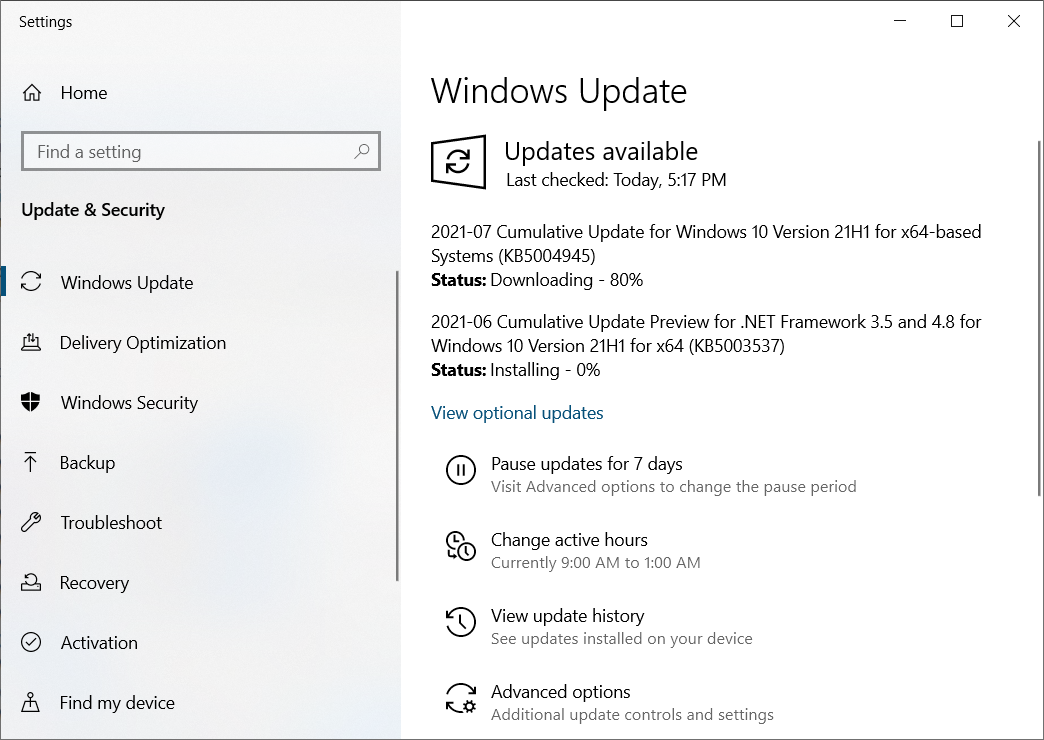
Detailed instructions on how to install these out-of-band security updates for your operating system, are available in the support documents linked below:
- Windows 10, version 21H1 (KB5004945)
- Windows 10, version 20H2 (KB5004945)
- Windows 10, version 2004 (KB5004945)
- Windows 10, version 1909 (KB5004946)
- Windows 10, version 1809 and Windows Server 2019 (KB5004947)
- Windows 10, version 1803 (KB5004949) [Not available yet]
- Windows 10, version 1507 (KB5004950)
- Windows 8.1 and Windows Server 2012 (Monthly Rollup KB5004954 / Security only KB5004958)
- Windows 7 SP1 and Windows Server 2008 R2 SP1 (Monthly Rollup KB5004953 / Security only KB5004951)
- Windows Server 2008 SP2 (Monthly Rollup KB5004955 / Security only KB5004959)
Security updates have not yet been released for Windows 10 version 1607, Windows Server 2016, or Windows Server 2012, but they will also be released soon, according to Microsoft.
"Release notes associated with these updates might publish with a delay of up to an hour after the updates are available for download," Microsoft said.
"Updates for the remaining affected supported versions of Windows will be released in the coming days."
Patch only fixes remote exploitation
The PrintNightmare vulnerability includes both a remote code execution (RCE) and a local privilege escalation (LPE) vector that can be used in attacks to run commands with SYSTEM privileges on a vulnerable system.
After Microsoft released the out-of-band update, security researcher Matthew Hickey verified that the patch only fixes the RCE and not the LPE component.
The Microsoft fix released for recent #PrintNightmare vulnerability addresses the remote vector - however the LPE variations still function. These work out of the box on Windows 7, 8, 8.1, 2008 and 2012 but require Point&Print configured for Windows 2016,2019,10 & 11(?). https://t.co/PRO3p99CFo
— Hacker Fantastic (@hackerfantastic) July 6, 2021
This means that the fix is incomplete and threat actors and malware can still locally exploit the vulnerability to gain SYSTEM privileges.
Mitigation also available
Microsoft urges customers to install these out-of-band security updates immediately to address the PrintNightmare vulnerability.
Those who cannot install these updates as soon as possible should check out the FAQ and Workaround sections in the CVE-2021-34527 security advisory for info on how to protect their systems from attacks exploiting this vulnerability.
The available mitigation options include disabling the Print Spooler service to remove printing capability locally and remotely or disabling inbound remote printing through Group Policy to remove remote attack vector by blocking inbound remote printing operations.
In the second case, Microsoft says that "the system will no longer function as a print server, but local printing to a directly attached device will still be possible."
CISA has also published a notification on the PrintNightmare zero-day last week encouraging admins to disable the Windows Print Spooler service on servers not used for printing.
Update 7/6/21: Added information about the incomplete fix.
Update 7/6/21 11:14 PM: Noted that KB5004949 is not available yet.


Comments
cpc6128 - 2 years ago
Unfortunately all links to microsoft are dead (http 404)
noelprg4 - 2 years ago
not dead anymore - working now on my end except for KB5004949 which does not exist and Win10 v1803 is out of support
remove link to KB5004949 as MS has not released this, sergiu
thepwrtank18 - 2 years ago
https://www.catalog.update.microsoft.com/Search.aspx?q=KB5004945 for the updates
noelprg4 - 2 years ago
those are for Win10 v2004, 20H2 & 21H1 only
older Windows versions have different KB updates
saluqi - 2 years ago
KB5004945 was installed on both my computers today. I am not well enough informed to know whether this problem affects my system. I have a WiFi-only home network: Internet wireless broadband receiver/modem, about 120 feet from house, connects to router (inside house) via Cat 7 Ethernet cable; router to "devices" (2 computers, 1 printer, one smartphone when within range) is wireless only. Router (Linksys EA7500) is inside house. Devices are about 25 feet from router, at opposite ends of the same large room; WiFi signal strength at the devices is around minus 45 dBm. Much less outside the house. Property is 10 acres, I have a very vigilant watchdog, its nearly impossible for anyone to approach the house closer than a quarter mile without my becoming aware of it. Such approaches are effectively limited to Amazon deliveries by UPS, or visits by people well known to me. This is ranch country, I am more than a mile outside the tiny local village. I am also handicapped and almost never away from the house.
I have the printer (Canon Pixma TS9120) and printer software (Canon) set up so if either computer sends a print job to the network print queue, the printer switches on, prints the job(s) and then presently switches off again, all automatically. That's all handled by the Canon software installed on the computers and on the printer itself.
So my somewhat naive question is, is my system potentially vulnerable to PrintNightmare attacks (in spite of KB5004945) and if so, in what form or how would that be observable?
The desktop computer is running Windows 10 Professional 64 bit, Version 21H1, build 19043.1083; the laptop is running Windows 10 Home 64 bit, Version 20H2, build 19042.1083. At last report (say an hour ago) the "print on demand" function was operating normally.
redwolfe_98 - 2 years ago
"KB5004945 was installed on both my computers today.
is my system potentially vulnerable to PrintNightmare attacks (in spite of KB5004945)."
the update protects one's computer from remote attacks. to my thinking, that is sufficient.
redwolfe_98 - 2 years ago
"I have a WiFi-only home network"
to secure your wireless router you should change the router's default password to your own unique password. also, disable "WiFi Protected Setup" in your router's settings.
survivor303 - 2 years ago
"kyocera" all again :D
saluqi - 2 years ago
It's not my first router; I always set them up with new unique passwords, never the default. Don't remember seeing a "WiFi Protected Setup" setting.
I remember "kyocera"
mrvg903 - 2 years ago
Windows 10, version 1909 (KB5004946) not installing on Windows 10 Pro. Backs out after reboot.