
A free master decryptor for the REvil ransomware operation has been released, allowing all victims encrypted before the gang disappeared to recover their files for free.
The REvil master decryptor was created by cybersecurity firm Bitdefender in collaboration with a trusted law enforcement partner.
While Bitdefender could not share details about how they obtained the master decryption key or the law enforcement agency involved, they told BleepingComputer that it works for all REvil victims encrypted before July 13th.
"As per our blog post, we received the keys from a trusted law enforcement partner, and unfortunately, this is the only information we are at liberty to disclose right now," Bitdefender's Bogdan Botezatu, Director of Threat Research and Reporting, told BleepingComputer.
"Once the investigation progresses and will come to an end, further details will be offered upon approval."
REvil ransomware victims can download the master decryptor from Bitdefender (instructions) and decrypt entire computers at once or specify specific folders to decrypt.
To test the decryptor, BleepingComputer encrypted a virtual machine with an REvil sample used in an attack earlier this year. After encrypting our files, we could use Bitdefender's decryptor to easily recover our files, as shown below.
Law enforcement likely compromised REvil servers
The REvil ransomware operation, aka Sodinokibi, is believed to be a rebrand or successor to the now "retired" ransomware group known as GandCrab.
Since launching in 2019, REvil has conducted numerous attacks against well-known companies, including JBS, Coop, Travelex, and Grupo Fleury.
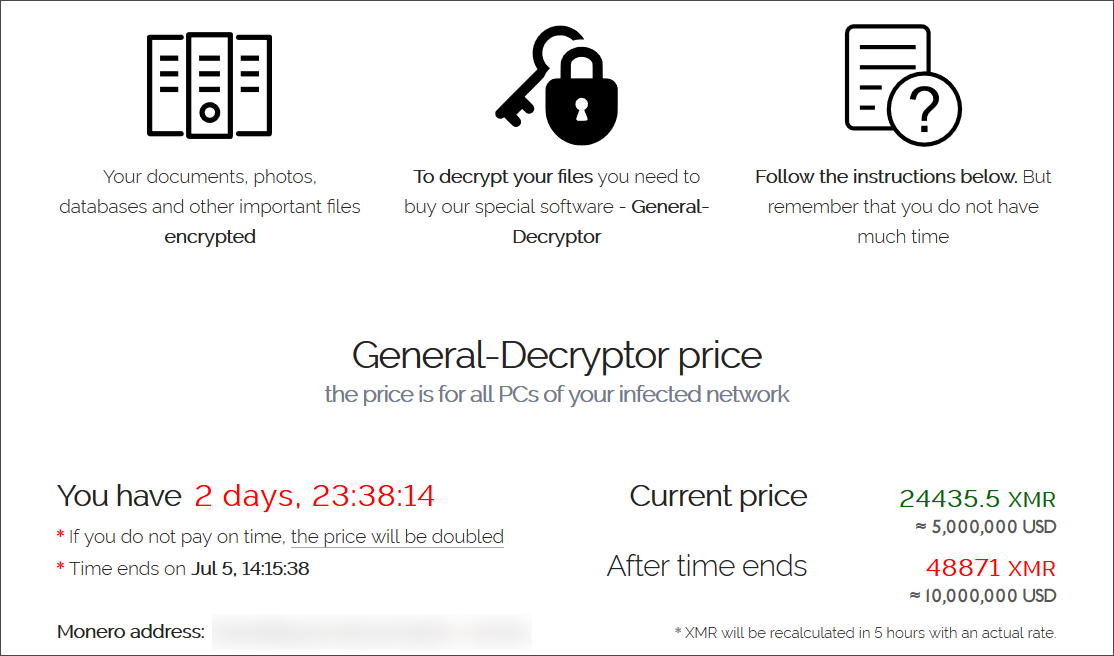
Finally, in a massive July 2nd attack using a Kaseya zero-day vulnerability, the ransomware gang encrypted sixty managed service providers and over 1,500 businesses worldwide.
After facing intense scrutiny by international law enforcement and increased political tensions between Russia and the USA, REvil suddenly shut down its operation on July 13th and disappeared.
While REvil was shut down, Kaseya mysteriously received a master decryptor for their attack, allowing MSPs and their customers to recover files for free.
As Bitdefender states that victims who REvil encrypted before July 13th can use this decryptor, it is safe to assume that the ransomware operation's disappearance was tied to this law enforcement investigation.
It is also likely that Kaseya obtaining the REvil master decryption key for the attack on their customers is also tied to the same investigation.
While REvil has returned to attacking victims earlier this month, the release of this master decryptor comes as a massive boon for existing victims who chose not to pay or simply couldn't after the ransomware gang disappeared.



Comments
navidas73 - 2 years ago
I'm really happy with this news. Sodinokibi has hit many companies and thereby threatened a large number of livelihoods. We will inform our customers immediately about the free decryptor.
It will be exciting to see how the REvil group continues. How do you feel about that, Lawrence?
Greetings - Janos from BeforeCrypt
yawnshard - 2 years ago
How about: Have a real backup strategy?
EmanuelJacobsson - 2 years ago
As the majority of ransomware targetting businesses leak data if not paid all it does is prevent extremely long downtimes, it doesnt take care of the fact your clients are now pissed of and your reputation badly damaged, and your employees and customers now will be targeted by spear phishing and brute force attacks.
yawnshard - 2 years ago
80% of ransomware victims suffer repeat attacks, according to new report
Source: CBS News
You simply, do not pay. Ever.
al1963 - 2 years ago
Yes, there is a decoding for another case other than Kaseya
Decryptor Started at Thu Sep 16 21:52:19 2021
This utility decrypts files encrypted by REvil ransomware.
This tool requires internet access!
NOTE: Certain versions of REvil are not yet decryptable.
Found the ransom note: Z:\test\revil\wy32wlj-readme.txt
Sending init request.
Done.
Sending intermediate request.
Done.
Decrypt Files ...
Decrypt [ 0] [G:\DATA\shifr\encode_files\Revil\SZ\kor_boot.ttf.wy32wlj] ... [OK]
Decrypt [ 1] [G:\DATA\shifr\encode_files\Revil\SZ\memtest.exe.wy32wlj] ... [OK]
Sending finish request.
Done.
Total decrypted files: [2]
Scan finished!
DG1991 - 2 years ago
We'll that's a blessing in disguise though. I hope it will do the same to the people who made the STOP DJVU Ransomware.
cfx69 - 2 years ago
New variant we've seen for the first time last night. kz6p51-readme.txt. The decryptor is not able to decrypt it.
Lawrence Abrams - 2 years ago
Decryptor can only recover files encrypted before July 13th.
Muhammad Ahmad - 1 year ago
Hi, Do you have any plan / idea either we will be able to get our files back which got encrypted with the same Revil ransomware in 2022?