
Today, T-Mobile customers said they could see other peoples' account and billing information after logging into the company's official mobile application.
According to user reports on social media, the exposed information included customers' names, phone numbers, addresses, account balances, and credit card details like the expiration dates and the last four digits.
As first reported by The Verge, some of the customers affected by this issue could see the sensitive information of multiple other people while logged into their own accounts.
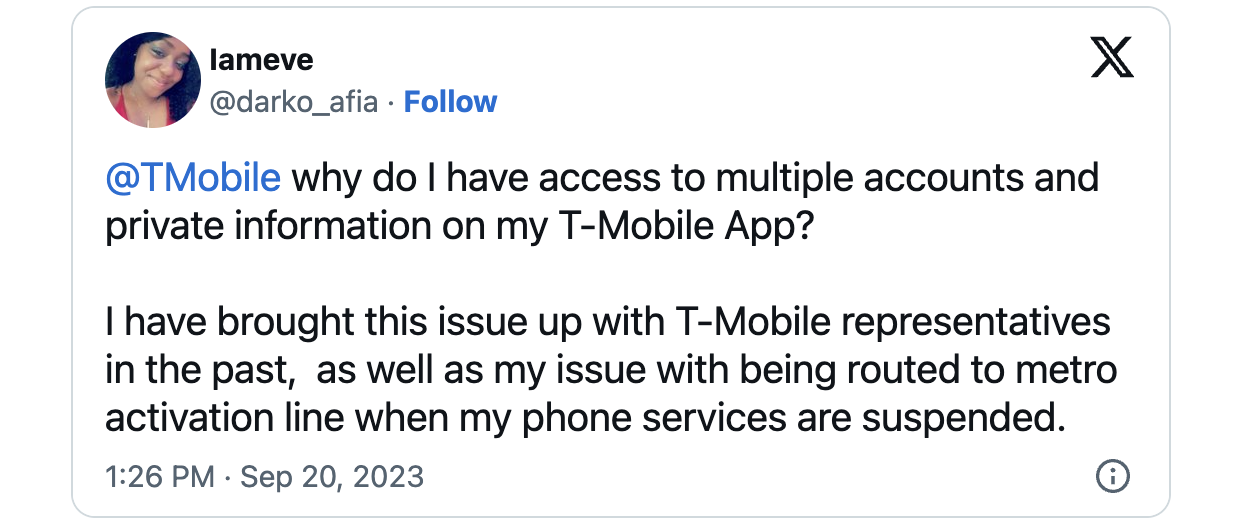
While a massive number of reports started surfacing earlier today on Reddit and Twitter, some T-Mobile customers also claimed that they've been experiencing this throughout the last two weeks.
"Reported this issue when it first popped up here on Reddit over 2 weeks ago and sent pics of the other person's info to their security team. No response, but wow, just wow," one customer said.
"I have brought this issue up with T-Mobile representatives in the past, as well as my issue with being routed to metro activation line when my phone services are suspended," another added.
T-Mobile says a cyberattack did not cause this incident, and its systems were not breached.
Also, despite the significant wave of customers reporting that they've been affected by this issue, T-Mobile says the incident had limited impact, only affecting less than 100 individuals.
"There was no cyberattack or breach at T-Mobile," a spokesperson told BleepingComputer when asked for more details.
"This was a temporary system glitch related to a planned overnight technology update involving limited account information for fewer than 100 customers, which was quickly resolved."
Nine data breaches since 2018
In May, T-Mobile disclosed the second data breach since the start of 2023 after hundreds of customers had their personal information exposed between late February and March after attackers hacked into the carrier's systems.
In January, the mobile carrier revealed another data breach after the sensitive info of 37 million customers was stolen using one of its Application Programming Interfaces (APIs).
Since 2018, T-Mobile has been hit by seven other data breaches:
- In August 2018, attackers accessed the data of around 3% of all T-Mobile customers.
- In 2019, T-Mobile exposed the account info of an undisclosed number of prepaid customers.
- In March 2020, T-Mobile employees were affected by a breach exposing their personal and financial information.
- In December 2020, threat actors accessed customer proprietary network info (phone numbers, call records).
- In February 2021, an internal T-Mobile app was accessed by unknown attackers without authorization.
- In August 2021, hackers brute-forced their way through T-Mobile's network following a breach of one of its testing environments.
- In April 2022, the notorious Lapsus$ extortion gang breached T-Mobile's network using stolen credentials.



Comments
GT500 - 7 months ago
T-Mobile just can't get their security together, can they?
bradleyross - 7 months ago
What I would want to know first if when they get the bad screen, is it simply a page that was supposed to go to another user. The second is whether they are using a Java-based application server to prepare the data. I have run into this problem several times, and it seems to be the same problem each time. In the Java classes for servlets, there is one object for the request, another for the response, and a third for the session.
Data related to a transaction needs to be attached to one of the data objects to have the correct scope. The class instance for handling transactions may be handling a number of the transactions at the same time, and it needs to use these data objects for the data to avoid different transactions overwriting the data.
If you you use instance variables in the servlet instance to store the data for transactions, the data can get overwritten between the time the data is obtained and when it is used to write the response. This is pass initial testing since you usually aren't having multiple transactions being processed at the same time. When it goes into full production, many transactions are being handled by a given object simultaneously and the problem becomes almost inevitable, although not all of the transactions will be affected.