The Link Between AWM Proxy & the Glupteba Botnet
Krebs on Security
JUNE 28, 2022
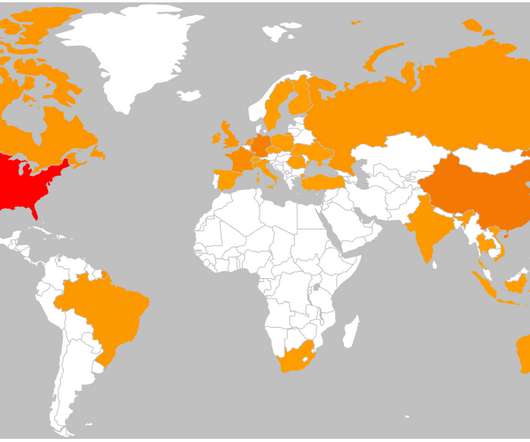
There is also ample evidence to suggest that Glupteba may have spawned Meris , a massive botnet of hacked Internet of Things (IoT) devices that surfaced in September 2021 and was responsible for some of the largest and most disruptive distributed denial-of-service (DDoS) attacks the Internet has ever seen. But on Dec. and starovikov[.]com.













Let's personalize your content