Analysis of Xloader’s C2 Network Encryption
Security Boulevard
JANUARY 21, 2022
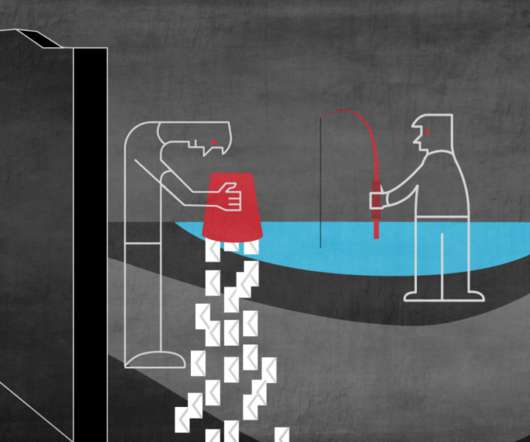
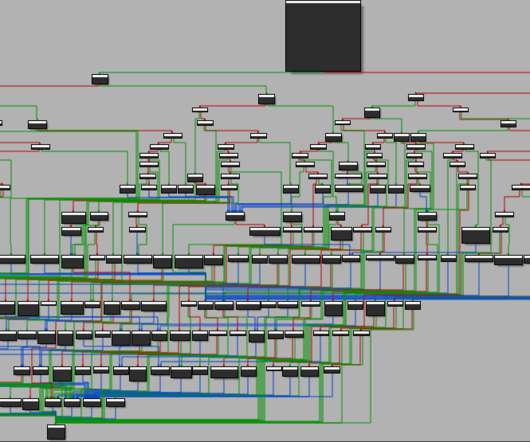
In October 2020, Formbook was rebranded as Xloader and some significant improvements were introduced, especially related to the command and control (C2) network encryption. In 2017, Formbook’s panel source was leaked, and subsequently, the threat actor behind Xloader moved to a different business model. Xloader PUSHEBP encrypted block.


























Let's personalize your content