A Deep Dive Into the Residential Proxy Service ‘911’
Krebs on Security
JULY 18, 2022
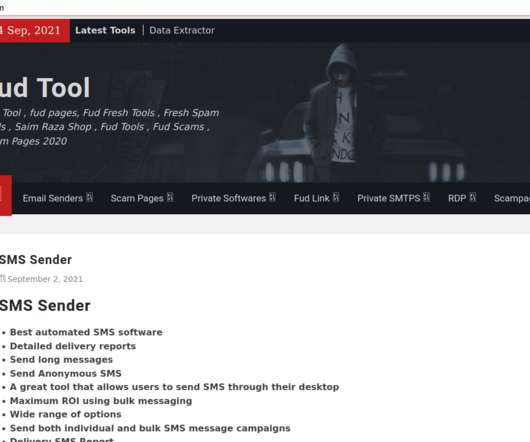
These two software are currently unknown to most if not all antivirus companies.” “Using the internal router, it would be possible to poison the DNS cache of the LAN router of the infected node, enabling further attacks.” The Exe Clean service made malware look like goodware to antivirus products. ”

















Let's personalize your content