On the Twitter Hack
Schneier on Security
JULY 20, 2020
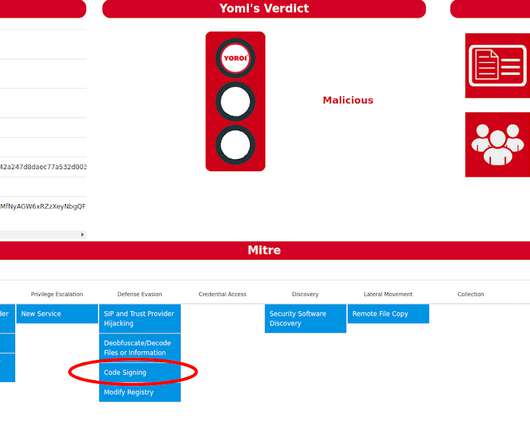
Twitter was hacked this week. Someone compromised the entire Twitter network, probably by stealing the log-in credentials of one of Twitter's system administrators. There are many security technologies companies like Twitter can implement to better protect themselves and their users; that's not the issue.






















Let's personalize your content