Why You Should Opt Out of Sharing Data With Your Mobile Provider
Krebs on Security
MARCH 20, 2023
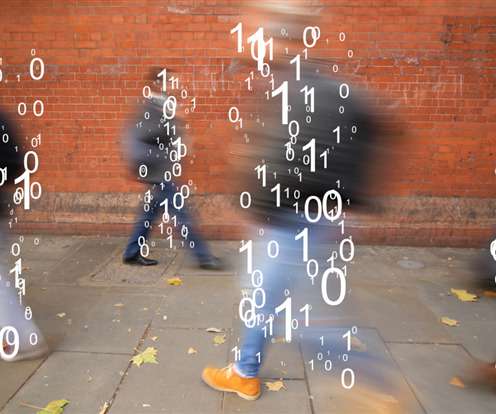
A new breach involving data from nine million AT&T customers is a fresh reminder that your mobile provider likely collects and shares a great deal of information about where you go and what you do with your mobile device — unless and until you affirmatively opt out of this data collection.









































Let's personalize your content