NIST’s ransomware guidelines look a lot like cyber resilience
Webroot
AUGUST 27, 2021
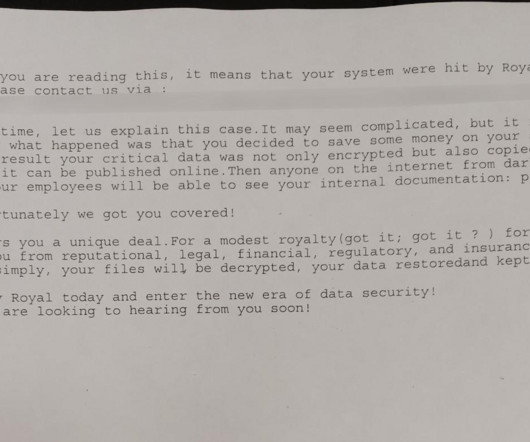
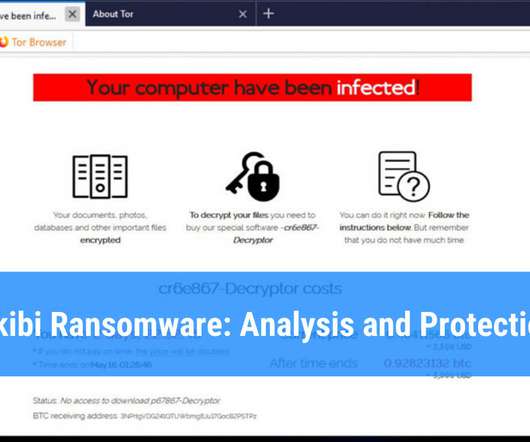
When the Institute for Security & Technology’s Ransomware Task Force published its report on combatting ransomware this spring, the Colonial Pipeline, JBS meatpacking and Kaseya VSA attacks were still around the corner. ” -Ransomware Task Force, IST. While many of these would fall to law enforcement, U.S.






























Let's personalize your content