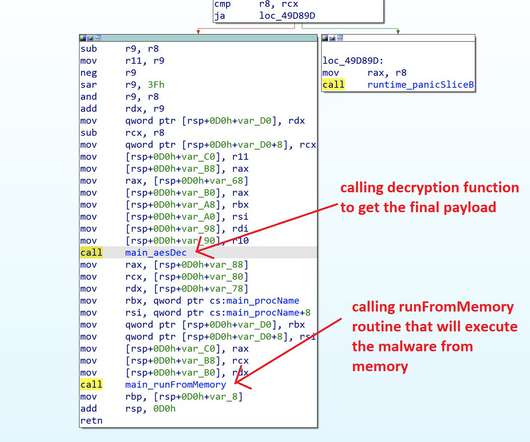
ViperSoftX uses more sophisticated encryption and anti-analysis techniques
Security Affairs
APRIL 29, 2023
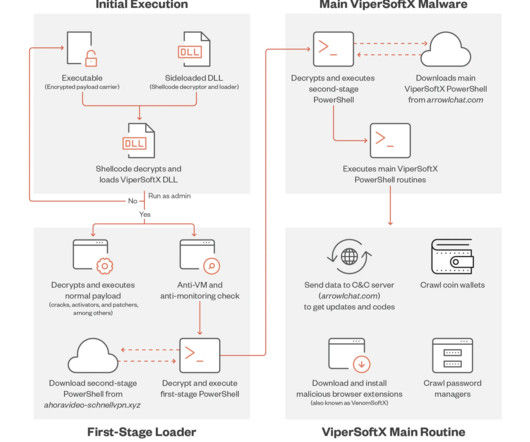
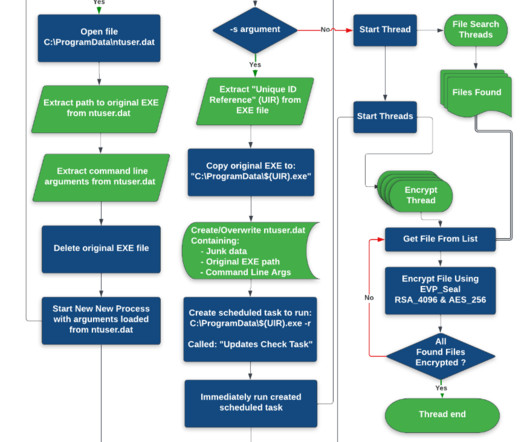
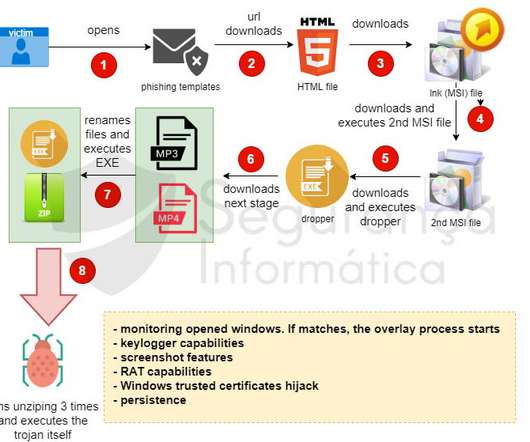
A new variant of the information-stealing malware ViperSoftX implements sophisticated techniques to avoid detection. Trend Micro researchers observed a new ViperSoftX malware campaign that unlike previous attacks relies on DLL sideloading for its arrival and execution technique. c2 arrowlchat[.]com c2 arrowlchat[.]com





































Let's personalize your content