Best Internet Security Suites & Software for 2022
eSecurity Planet
FEBRUARY 4, 2022
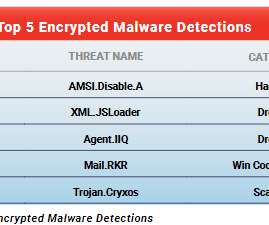
Malware is one of the biggest threats businesses face, and with nearly a third of all malware coming through the internet and email, businesses and consumers alike need ways to protect themselves. This guide covers the major categories of internet security suites and includes a few of the top options for each. Antivirus Software.
















































Let's personalize your content