Giant health insurer struck by ransomware didn't have antivirus protection
Malwarebytes
OCTOBER 11, 2023
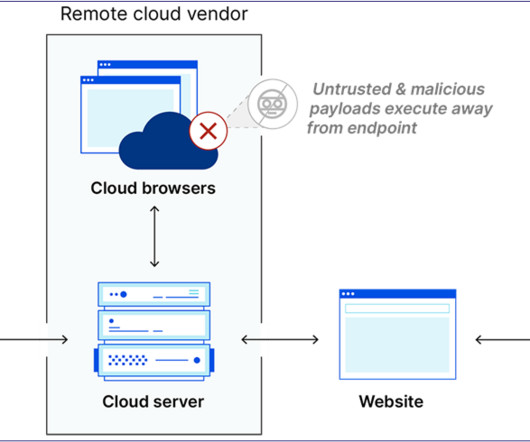
The Philippine Health Insurance Corporation (PhilHealth), has confirmed that it was unprotected by antivirus software when it was attacked by the Medusa ransomware group in September. Stop malicious encryption. Their data is now available for download on the dark web. Use EDR or MDR to detect unusual activity before an attack occurs.

















Let's personalize your content