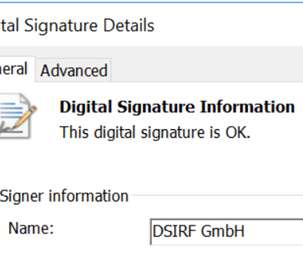
European firm DSIRF behind the attacks with Subzero surveillance malware
Security Affairs
JULY 28, 2022
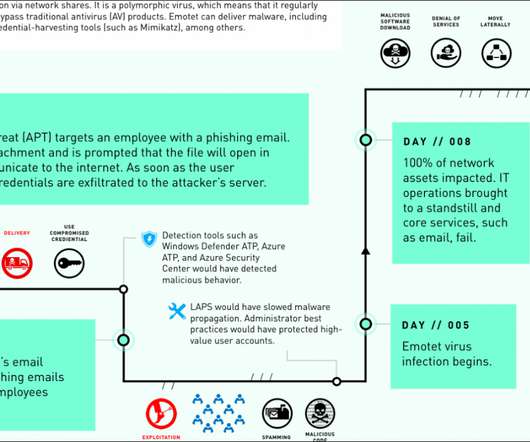
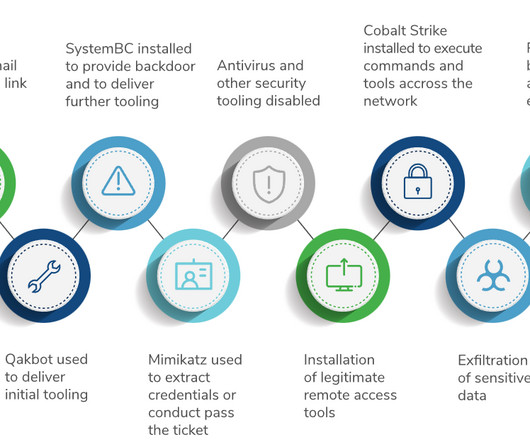
The Microsoft Threat Intelligence Center (MSTIC) and the Microsoft Security Response Center (MSRC) researchers linked a threat group known as Knotweed to an Austrian surveillance firm named DSIRF, known for using multiple Windows and Adobe zero-day exploits. SecurityAffairs – hacking, Subzero malware). ” concludes Microsoft.




















Let's personalize your content