How to Accelerate Government Transformation by Reducing Risk, Complexity, and Cost
Thales Cloud Protection & Licensing
JUNE 27, 2022
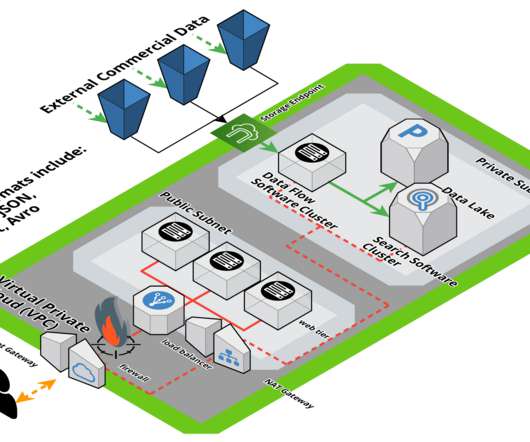
How to Accelerate Government Transformation by Reducing Risk, Complexity, and Cost. The days of dreadful long lines at crowded and inefficient government agencies may be coming to an end. Digitalization of services and adoption of new platforms are reinventing government services and public administration.























Let's personalize your content