Attacks Escalating Against Linux-Based IoT Devices
eSecurity Planet
JANUARY 20, 2022
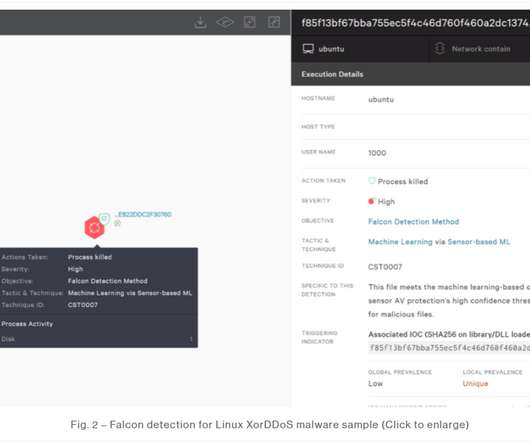
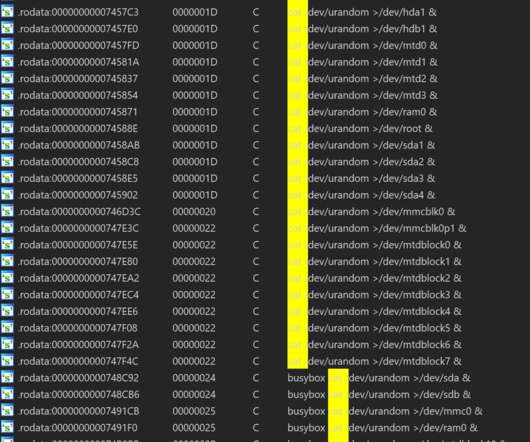
Incidents of malware targeting Linux-based Internet of Things (IoT) devices jumped by more than a third in 2021, with three malware families the primary drivers behind the increase. That echoes similar reports that have shown an increase in DDoS attacks worldwide. Also read: Top 8 DDoS Protection Service Providers for 2022.
























Let's personalize your content