Log4Shell Vulnerability is the Coal in our Stocking for 2021
McAfee
DECEMBER 10, 2021
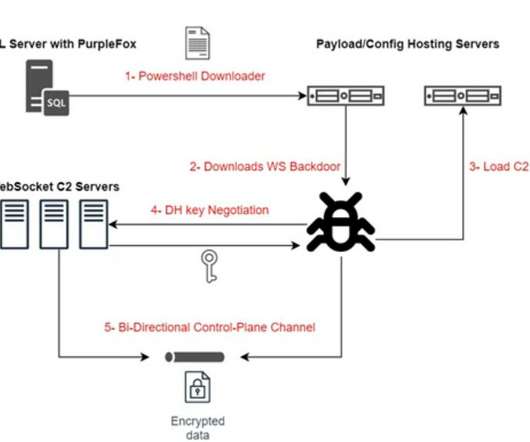
The most popular lookup currently being seen in both PoCs and active exploitation is utilizing LDAP; however, other lookups such as RMI and DNS are also viable attack vectors. This was done using the public Docker container , and a client/server architecture leveraging both LDAP and RMI, along with marshalsec to exploit log4j version 2.14.1.













































Let's personalize your content