Network Security Architecture: Best Practices & Tools
eSecurity Planet
APRIL 26, 2024
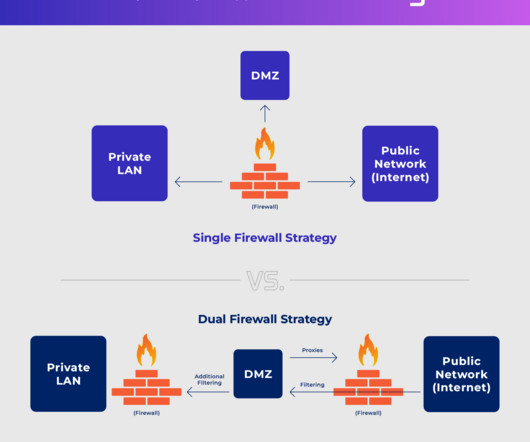
Network security architecture is a strategy that provides formal processes to design robust and secure networks. This article explores network security architecture components, goals, best practices, frameworks, implementation, and benefits as well as where you can learn more about network security architecture.















































Let's personalize your content