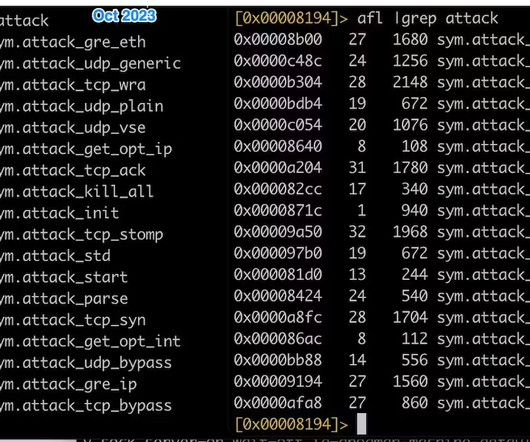
Keycloak Patches Vulnerabilities, Mitigates DDoS and Data Theft Risks
Penetration Testing
APRIL 18, 2024
Keycloak, a widely used open-source solution for authentication and authorization, has released important security updates addressing multiple vulnerabilities.




































Let's personalize your content