9 Best Penetration Testing Tools for 2022
eSecurity Planet
FEBRUARY 24, 2022
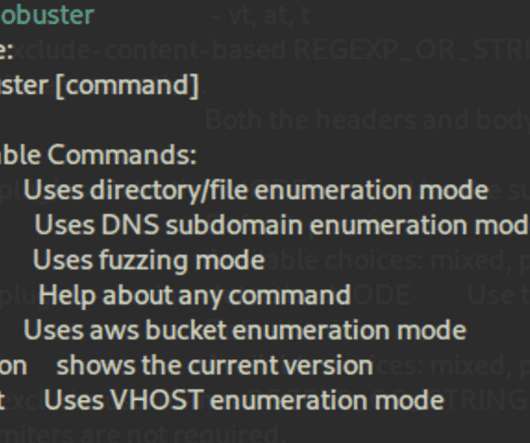
When shopping for a penetration testing tool, be aware that you will likely need several components to perform a complete penetration test. There are a number of complementary technologies often used by organizations to address security holes. Can spot backup and configuration files. Can hide status and process (e.g.,










Let's personalize your content