Protecting Big Data, while Preserving Analytical Agility
Thales Cloud Protection & Licensing
NOVEMBER 19, 2018
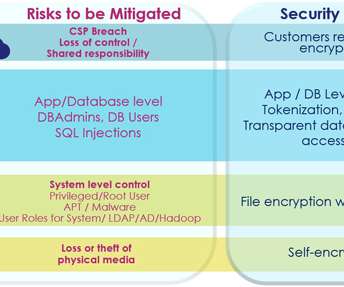
The age of Big Data is upon us. And, as more data is available for analytical purposes, more sensitive and private information is at risk. Protecting the confidentiality and integrity and of warehoused data and ensuring that access is controlled is vital to keeping that data secure. respondents.”.



































Let's personalize your content