GUEST ESSAY: A primer on best practices for automating supply chain cybersecurity
The Last Watchdog
OCTOBER 16, 2023
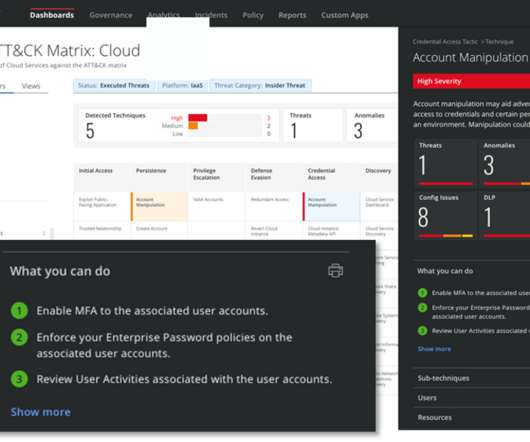
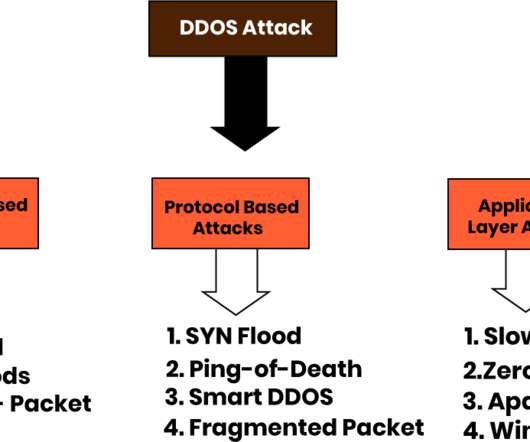
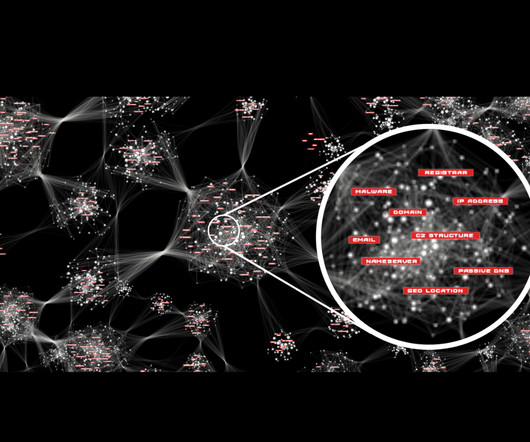
In response, industry professionals must automate their cybersecurity tools to stay ahead. The 2020 SolarWinds cybersecurity incident — which industry experts call the supply chain attack of the decade — was an incredibly high-profile breach affecting massive corporations. Simply put, cyberattacks are on the rise.
































Let's personalize your content