Guide to ransomware and how to detect it
IT Security Guru
SEPTEMBER 28, 2023
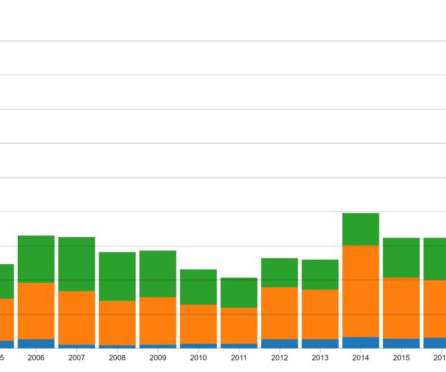
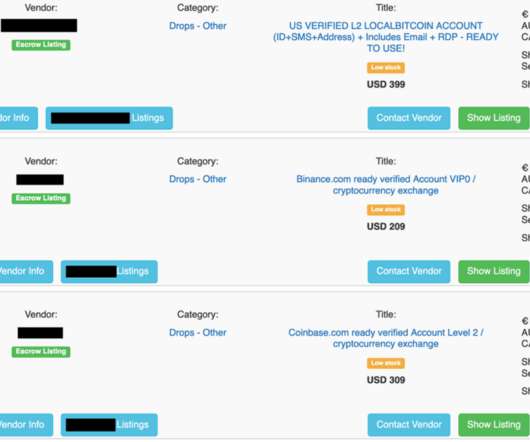
The landscape of ransomware has undergone rapid evolution, shifting from a relatively straightforward form of malicious software primarily affecting individual computer users, to a menacing enterprise-level threat that has inflicted substantial harm on various industries and government institutions.











































Let's personalize your content