How 5G network is immune to Cyber Attacks
CyberSecurity Insiders
MAY 7, 2023
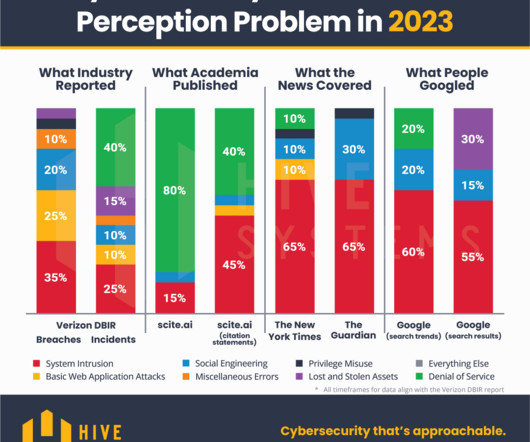
It is not accurate to say that 5G networks are completely immune to cyber attacks. Like any other network, 5G networks are vulnerable to various types of cyber attacks, such as distributed denial-of-service (DDoS) attacks, phishing attacks, and malware infections.







































Let's personalize your content