Cybersecurity Event Cancelled After Being Hit By Cybercriminals
Joseph Steinberg
OCTOBER 24, 2022
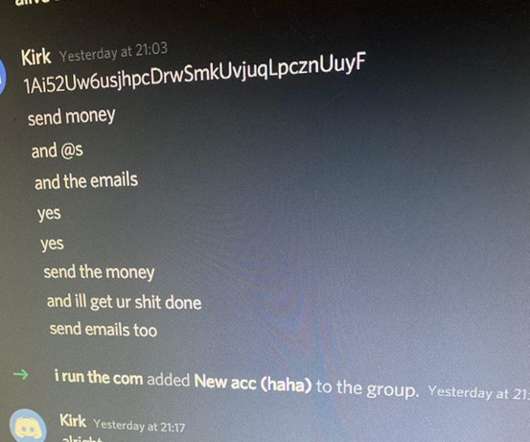
An online cybersecurity event with 2,500 people already logged in had to be cancelled after suspected cybercriminals launched a social engineering attack in the event’s chat window. Shortly after such messages appeared, the AICD, in order to protect attendees, cancelled the event, and contacted local law enforcement.










































Let's personalize your content