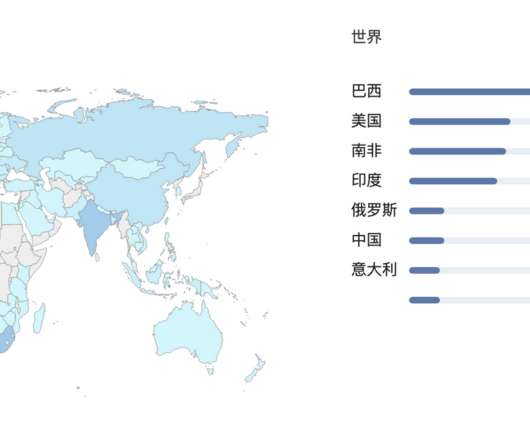
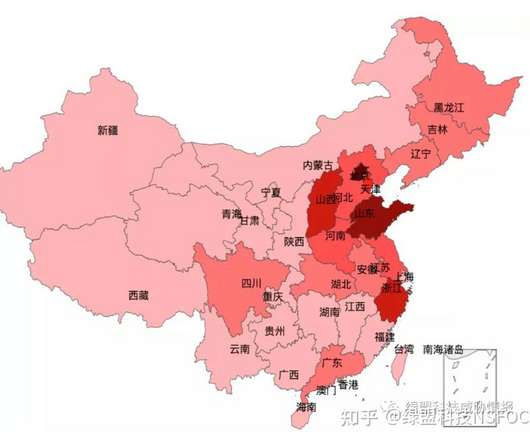
Overview of IoT threats in 2023
SecureList
SEPTEMBER 21, 2023
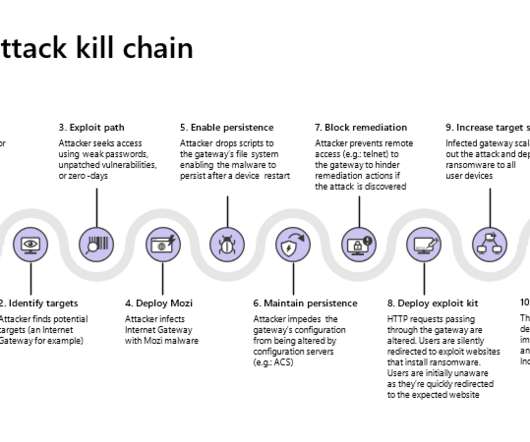
The first-ever large-scale malware attacks on IoT devices were recorded back in 2008, and their number has only been growing ever since. A successful password cracking enables hackers to execute arbitrary commands on a device and inject malware. Starts ~50 browser instances per Windows PC which evade any anti-DDoS defense.

















Let's personalize your content