How Secure Is Cloud Storage? Features, Risks, & Protection
eSecurity Planet
JANUARY 18, 2024
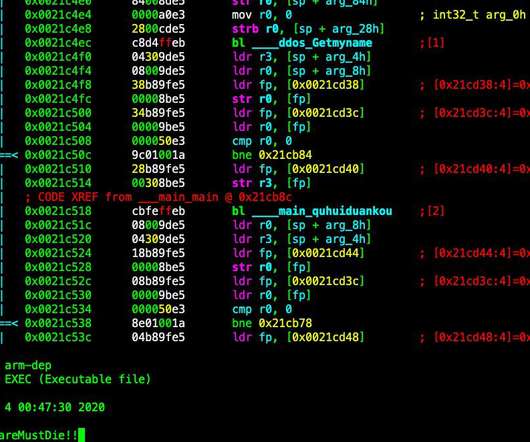
Cloud Storage Security Risks Despite its obvious benefits, cloud storage still faces common challenges, including misconfiguration, data breaches, insecure interface, unauthorized access, DDoS attacks, insider threats, lack of control, encryption problems, patching issues, compliance, and monitoring issues.











































Let's personalize your content