Best Distributed Denial of Service (DDoS) Protection Tools
eSecurity Planet
JANUARY 14, 2022
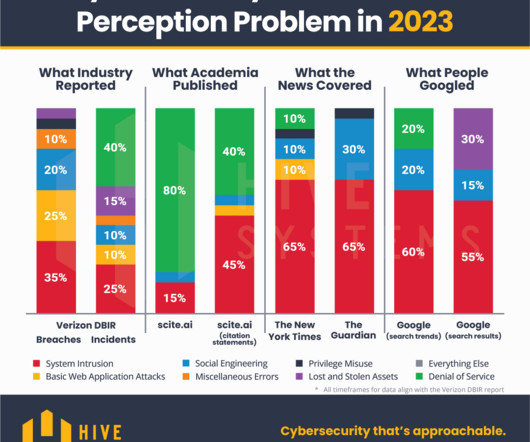
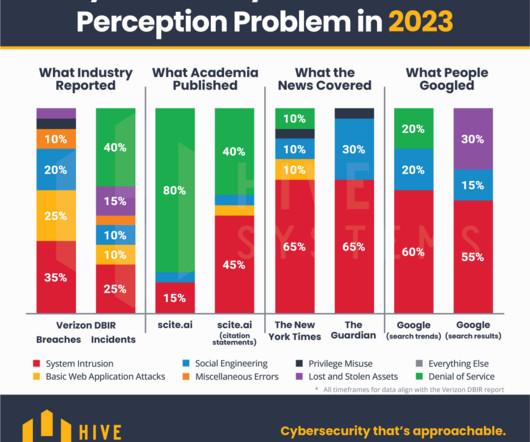
Distributed denial of service (DDoS) attacks can cripple an organization, a network, or even an entire country, and they show no sign of slowing down. DDoS attacks may only make up a small percentage of security threats, but their consequences can be devastating. According to Imperva Research Labs, DDoS attacks tend to come in waves.


























Let's personalize your content