Moobot Botnet Chews Up Hikvision Surveillance Systems
Threatpost
DECEMBER 8, 2021
Attackers are milking unpatched Hikvision video systems to drop a DDoS botnet, researchers warned.

Threatpost
DECEMBER 8, 2021
Attackers are milking unpatched Hikvision video systems to drop a DDoS botnet, researchers warned.
Security Affairs
FEBRUARY 19, 2023
Twitter will allow using the SMS-based two-factor authentication (2FA) only to its Blue subscribers GoDaddy discloses a new data breach Fortinet fixes critical vulnerabilities in FortiNAC and FortiWeb German airport websites hit by DDos attacks once again Cisco fixed critical RCE bug in ClamAV Open-Source Antivirus engine CISA adds Cacti, Office, Windows (..)
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
FEBRUARY 11, 2024
Now Cybersecurity expert says the next generation of identity theft is here: ‘Identity hijacking’ Were 3 Million Toothbrushes Really Used for a DDoS Attack? Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, newsletter)

SecureList
SEPTEMBER 21, 2023
The first-ever large-scale malware attacks on IoT devices were recorded back in 2008, and their number has only been growing ever since. A successful password cracking enables hackers to execute arbitrary commands on a device and inject malware. Starts ~50 browser instances per Windows PC which evade any anti-DDoS defense.
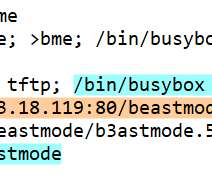
Security Affairs
APRIL 2, 2022
Operators behind the Mirai-based distributed denial-of-service (DDoS) botnet Beastmode (aka B3astmode) added exploits for Totolink routers. The Mirai -based distributed denial-of-service (DDoS) botnet Beastmode (aka B3astmode) now includes exploits for Totolink routers. CVE-2017-17215 targets Huawei HG532 routers.

Security Affairs
AUGUST 7, 2022
Greek intelligence service used surveillance malware to spy on a journalist, Reuters reports Slack resets passwords for about 0.5% Greek intelligence service used surveillance malware to spy on a journalist, Reuters reports Slack resets passwords for about 0.5% Pierluigi Paganini.

Security Affairs
APRIL 17, 2020
Syrian-linked APT group SEA recently used COVID-19-themed lures as part of a long-running surveillance campaign, security researchers warn. Notably, the C2 servers of SilverH awk , an Android malware family previously reported on by Lookout researchers, were located on IP addresses belonging to STE.” The experts conclude.”It
Let's personalize your content