DNS-over-HTTP/3 in Android
Google Security
JULY 19, 2022
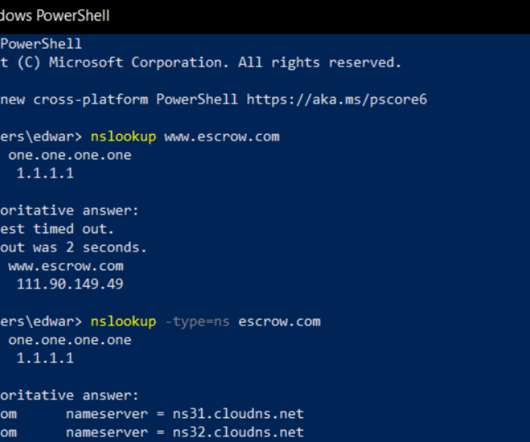
Posted by Matthew Maurer and Mike Yu, Android team To help keep Android users’ DNS queries private, Android supports encrypted DNS. In addition to existing support for DNS-over-TLS, Android now supports DNS-over-HTTP/3 which has a number of improvements over DNS-over-TLS. In Android 9.0,



































Let's personalize your content