Iranian hackers target energy sector with new DNS backdoor
Bleeping Computer
JUNE 10, 2022
The Iranian Lycaeum APT hacking group uses a new.NET-based DNS backdoor to conduct attacks on companies in the energy and telecommunication sectors. [.].

Bleeping Computer
JUNE 10, 2022
The Iranian Lycaeum APT hacking group uses a new.NET-based DNS backdoor to conduct attacks on companies in the energy and telecommunication sectors. [.].
Security Affairs
JUNE 11, 2022
Iran-linked Lyceum APT group uses a new.NET-based DNS backdoor to target organizations in the energy and telecommunication sectors. The Iran-linked Lyceum APT group, aka Hexane or Spilrin, used a new.NET-based DNS backdoor in a campaign aimed at companies in the energy and telecommunication sectors, ZScaler researchers warn.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
MAY 1, 2024
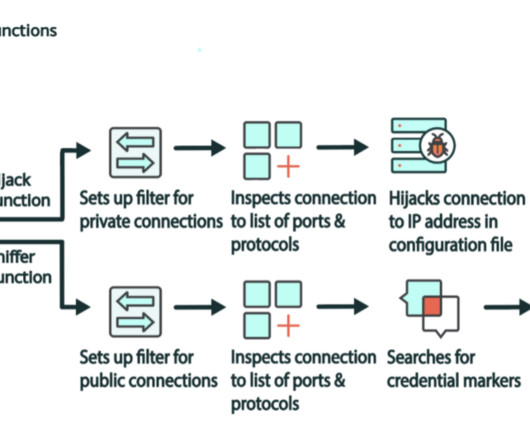
The malicious code can also perform DNS and HTTP hijacking within private IP spaces. “What makes this malware family so insidious is the ability to perform HTTP and DNS hijacking for connections to private IP addresses. Additionally, it can interact with other devices on the LAN and transfer data or deploy new agents.

Security Affairs
OCTOBER 20, 2021
China-linked cyberespionage group LightBasin hacked mobile telephone networks around the world and used specialized tools to access calling records. CrowdStrike researchers reported that at least 13 telecommunication companies were compromised by since 2019. ” reads the report published by Crowdstrike.

Security Affairs
JANUARY 23, 2019
DHS has issued a notice of a CISA emergency directive urging federal agencies of improving the security of government-managed domains (i.e.gov) to prevent DNS hijacking attacks. The notice was issued by the DHS and links the emergency directive Emergency Directive 19-01 titled “Mitigate DNS Infrastructure Tampering.”.
Security Affairs
SEPTEMBER 21, 2022
Russia-linked APT group Sandworm has been observed impersonating telecommunication providers to target Ukrainian entities with malware. Russia-linked cyberespionage group Sandworm has been observed impersonating telecommunication providers to target Ukrainian entities with malware. SecurityAffairs – hacking, Log4Shell).

CyberSecurity Insiders
OCTOBER 22, 2021
CrowdStrike security researchers have discovered that a hacking group dubbed LightBasin aka UNC1945 has been hiding in the networks of renowned telecom networks from the past 5 years, monitoring all their business operations and sending censorious data to remote servers.
Let's personalize your content