Post-Quantum Cryptography: Lessons Learned from SHA-1 Deprecation
Security Boulevard
JULY 21, 2022
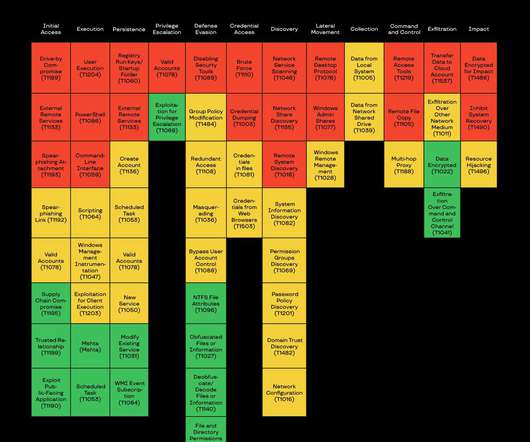
For businesses still using the broken SHA-1, they were facing serious risks , including: Increased possibility of a collision or man-in-the-middle attack. NIST has developed a whitepaper which outlines the steps for migration to post-quantum cryptography. Post-Quantum Encryption Algorithms Announced. Crypto-agility.





















Let's personalize your content