Thinking About the Future of InfoSec (v2022)
Daniel Miessler
MARCH 20, 2022
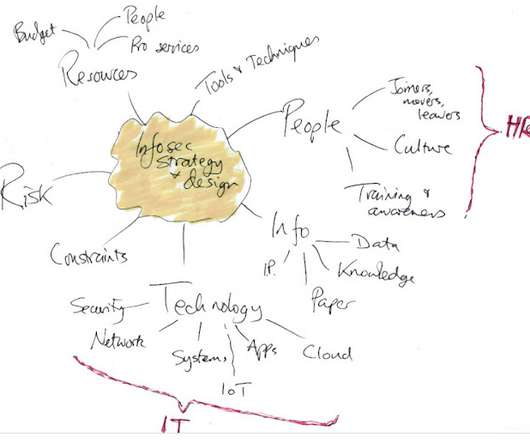
The ideas will cover multiple aspects of InfoSec, from organizational structure to technology. Technology. At the highest level, I think the big change to InfoSec will be a loss of magic compared to now. Technology. HT to Jeremiah Grossman to also being very early to seeing the role of insurance in InfoSec.







































Let's personalize your content