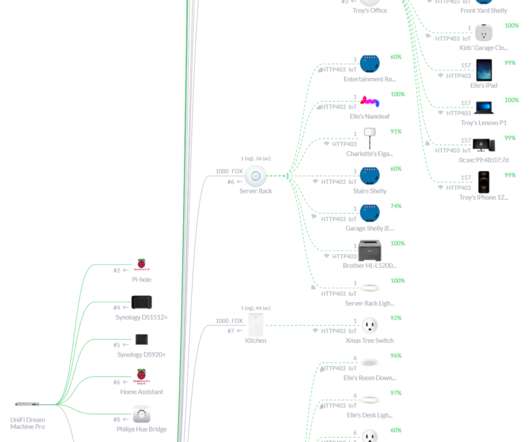
IoT Unravelled Part 2: IP Addresses, Network, Zigbee, Custom Firmware and Soldering
Troy Hunt
NOVEMBER 23, 2020
I'm not ashamed to say that the process of getting even the basics working absolutely did my head in as I waded through a sea of unfamiliar technologies, protocols and acronyms. So, peeling back that next layer, the whole IoT space isn't just about devices that get their own IP address on your network and talk over TCP (or UDP).













































Let's personalize your content