Android malware, Android malware and more Android malware
SecureList
MARCH 20, 2024
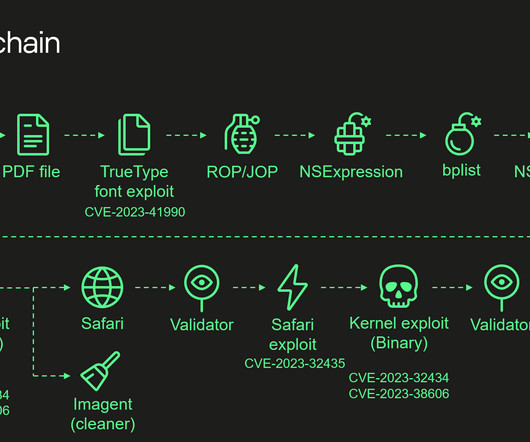
Introduction Malware for mobile devices is something we come across very often. million malware, adware, and riskware attacks on mobile devices. Among the mobile platforms, Android remains the most popular target operating system for cybercriminals. In 2023 , our technologies blocked 33.8 and sends it to the C2.


























Let's personalize your content