Sophisticated Social Engineering Campaign Linked to Black Basta Ransomware
Penetration Testing
MAY 13, 2024
Rapid7 analysts have uncovered a new, highly targeted social engineering campaign potentially linked to the Black Basta ransomware group.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Penetration Testing
MAY 13, 2024
Rapid7 analysts have uncovered a new, highly targeted social engineering campaign potentially linked to the Black Basta ransomware group.
Penetration Testing
APRIL 17, 2024
McAfee Labs researchers have uncovered a dangerous new variant of the Redline Stealer malware that uses clever obfuscation tactics and aggressive social engineering to trick victims and evade detection.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Penetration Testing
MARCH 6, 2024
Threat actors (TAs) are weaponizing a combination of social engineering, phishing infrastructure, and an advanced Android banking trojan to... The post Copybara Fraud Campaign Leverages On-Device Fraud and Social Engineering Tactics appeared first on Penetration Testing.

CyberSecurity Insiders
MARCH 28, 2023
Attack simulation and penetration testing are both methods used to identify vulnerabilities in a company’s cybersecurity infrastructure, but there are some differences between the two. The post Understanding the difference between attack simulation vs penetration testing appeared first on Cybersecurity Insiders.

Penetration Testing
MAY 15, 2024
This nefarious scheme involves a novel tactic of exploiting Microsoft’s Quick Assist, a legitimate remote assistance tool, to gain... The post Storm-1811 Exploits Quick Assist for Social Engineering, Paving Way for Black Basta Ransomware appeared first on Penetration Testing.

CyberSecurity Insiders
JANUARY 28, 2022
For many businesses, penetration testing is an important part of their security protocol. However, penetration testing can be costly and difficult to find the right service for your needs. However, penetration testing can be costly and difficult to find the right service for your needs. Duration of the test.

SecureWorld News
JUNE 28, 2020
With many organizations now planning their annual penetration tests ("pentest" for short), a change is needed in order to accommodate remote workers. It also begs what are you allowed to test versus what is now considered taboo considering end-users may be operating with their own personal equipment?

Penetration Testing
DECEMBER 19, 2023
Sophos X-Ops is warning the hospitality industry that the “Inhospitality” malspam campaign represents a cunning blend of social engineering and malware, specifically targeting the hospitality industry.

Penetration Testing
MARCH 6, 2024
A Cybereason Security Services analysis uncovers a sophisticated infostealer campaign that leverages GitHub, GitLab, Telegram, and common social engineering tactics to compromise victims.

CyberSecurity Insiders
MAY 28, 2023
Malware Analysis: Explore malware types, their behavior, and the techniques used for analyzing and detecting them. Investigate malware’s propagation methods, evasion techniques, and methods for identifying and mitigating potential threats.

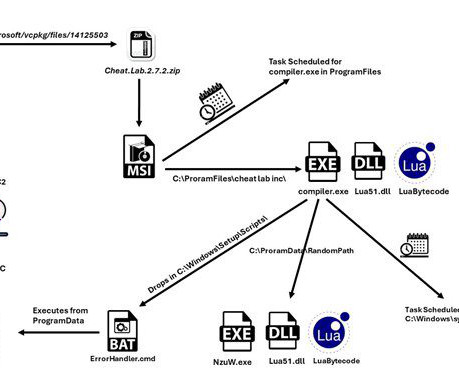
Hot for Security
APRIL 19, 2021
Notorious FIN7 gang stole payment card details from retailers around the world Cybercrime gang posed as penetration testing firm to recruit hackers. More details on how the malware operated can be read about in this technical paper by Bitdefender Labs. Gorman of the Western District of Washington. ”

CyberSecurity Insiders
DECEMBER 14, 2021
The event will also witness a host of demos and sessions from top cybersecurity experts who will be ready to offer a knowledge share on topics such as Blockchain Technology’s usage in security field, adversary emulation, cloud assessment, mobile malware, penetration testing, Red Teaming, Threat Hunting, Social Engineering and Web Apps.

Hot for Security
JUNE 25, 2021
In a typical attack, boobytrapped emails would be sent to targeted companies posing as legitimate communications through cunning use of social engineering. If the recipient opened the included attachment, their computer would be infected by a version of the Carbanak malware.

eSecurity Planet
JUNE 20, 2023
After surveying trusted penetration testing sources and published pricing, the cost of a penetration test for the average organization is $18,300. and different types of penetration tests (black box, gray box, white box, social engineering, etc.).
eSecurity Planet
FEBRUARY 21, 2023
A red team’s activity can extend beyond cybersecurity attacks and vulnerability scanning to include phishing , social engineering , and physical compromise campaigns lasting weeks or more. The red team literally tests the effectiveness of the organization’s defensive measures — often without warning.

CyberSecurity Insiders
OCTOBER 14, 2021
This gang of cybercriminals targets individuals within an organization with social engineering tactics designed to fool them into opening a document from a ZIP file attached to an email. How do hackers use social engineering? Social engineering schemes range from covert to obvious. OnePercent Group attacks.

Security Affairs
SEPTEMBER 15, 2022
Threat actors used employees’ publicly-available Personally Identifiable Information (PII) and social engineering techniques to impersonate victims and obtain access to files, healthcare portals, payment information, and websites. Well-maintained anti-virus and anti-malware software may prevent commonly used attacker tools.
Security Affairs
JANUARY 28, 2023
The LockBit Locker group is known for using a combination of advanced techniques, even phishing, and also social engineering, to gain initial access to a company’s network. The gang was one of the first gangs operating double extortion practices and supporting such attacks with dedicated toolkits such as the Stealbit malware.

Security Boulevard
DECEMBER 19, 2022
setting the foundations for successful targeted malware and exploits serving campaigns. Sample uses of these stolen and compromised databases includes: - setting the foundation for a successful spear-phishing campaigns. setting the foundations for successful widespread spam and botnet propagation campaigns.

ForAllSecure
APRIL 26, 2023
Common Types of Cyber Attacks Common techniques that criminal hackers use to penetrate systems include social engineering, password attacks, malware, and exploitation of software vulnerabilities. Malware can be delivered through email attachments, malicious websites, or compromised software.
SecureWorld News
MARCH 1, 2023
Thinking like a fraudster can help create additional barriers for these social engineering tricks and form a foundation for effective security awareness training so that the human factor hardens an organization's defenses instead of being the weakest link. Yet another step in prepping for the attack is to proofread the email.

SecureList
FEBRUARY 10, 2023
Penetration testing is something that many (of those who know what a pentest is) see as a search for weak spots and well-known vulnerabilities in clients’ infrastructure, and a bunch of copied-and-pasted recommendations on how to deal with the security holes thus discovered.

Herjavec Group
MAY 19, 2022
Segment your internal corporate networks to isolate any malware infections that may arise. Conduct regular social engineering tests on your employees to actively demonstrate where improvements need to be made. Conduct regular network penetration tests to identify flaws and vulnerabilities in your corporate networks.

eSecurity Planet
NOVEMBER 18, 2021
Most operations use payloads, but there are a few payload-less attacks, such as phishing campaigns that do not include malicious links or malware , but rely on more sophisticated deception such as spoofing to trick their targets. Most attacks will make the victim click on something that installs malware or redirects to a fake website.

Hot for Security
JUNE 25, 2021
In a typical attack, boobytrapped emails would be sent to targeted companies posing as legitimate communications through cunning use of social engineering. If the recipient opened the included attachment, their computer would be infected by a version of the Carbanak malware.

Zigrin Security
OCTOBER 11, 2023
For a detailed threat actor description do not forget to check out our blog article about selecting between black-box, white-box, and grey-box penetration tests and also you would know which pentest you need against a specific threat actor. Regularly conduct cybersecurity training sessions to reinforce good security habits.

CyberSecurity Insiders
JANUARY 18, 2022
The same symptoms will occur in your IT environment as the malware spreads downloading data and expanding across your global network corrupting backups and leaving little options. Social engineering. Social engineering is the most prevalent way threat actors find their way into your environment.

Malwarebytes
MAY 23, 2023
Create policies to include cybersecurity awareness training about advanced forms of social engineering for personnel that have access to your network. CISA consider the following to be advanced forms of social engineering: Search Engine Optimization (SEO) poisoning. Drive-by-downloads. Malvertising.

NopSec
AUGUST 16, 2022
Most cyber attacks are carried out using a combination of social engineering, phishing emails, and vulnerabilities — Java, Adobe Flash and Acrobat, Firefox and Chrome plugins, 0-day client-side / browser vulnerabilities. Critical Security Control 10: Malware Defenses Malware remains a dangerous threat to organizations of all sizes.

Security Affairs
AUGUST 27, 2019
Using compromised accounts, the threat actors send spearphishing emails with malicious Excel attachments to deliver the DanBot malware, which subsequently deploys post-intrusion tools.” The threat actors carried out spearphishing attacks using weaponized Excel attachments to deliver the DanBot malware.

The Last Watchdog
JUNE 21, 2020
Balaban This ransomware was doing the rounds over spam generated by the Gameover ZeuS botnet, which had been originally launched in 2011 as a toolkit for stealing victim’s banking credentials and was repurposed for malware propagation. These included PClock, CryptoLocker 2.0, Crypt0L0cker, and TorrentLocker.

SecureList
NOVEMBER 22, 2022
Unlike common stealers, this malware gathered data that can be used to identify the victims, such as browsing histories, social networking account IDs and Wi-Fi networks. This has become a real stand-alone business in the dark web ( Malware-as-a-Service , MaaS). ATM and PoS malware to return with a vengeance.

CyberSecurity Insiders
JUNE 7, 2023
A report reveals various cyber-attacks that often target small businesses, such as malware, phishing, data breaches, and ransomware attacks. Also, small businesses are vulnerable to malware, brute-force attacks, ransomware, and social attacks and may not survive one incident.

Malwarebytes
MAY 19, 2022
These may be obtained by phishing, social engineering, insider threats, or carelessly handed data. Malware is packed in certain ways to avoid detection and identification. Penetration testing can expose misconfigurations with services listed above such as cloud, VPNs, and more. Valid accounts.

Security Affairs
AUGUST 10, 2018
Security experts at Trustwave have released Social Mapper, a new open-source tool that allows finding a person of interest across social media platform using facial recognition technology. Recent statistics show social media users are more than twice as likely to click on links and open documents compared to those delivered via email.

eSecurity Planet
SEPTEMBER 10, 2021
What are the results of the provider’s most recent penetration tests? Comprehensive training should include basic security knowledge like how to create a strong password and identify possible social engineering attacks as well as more advanced topics like risk management. Conduct audits and penetration testing.

SecureList
APRIL 15, 2024
If the attacker knows their way around the target infrastructure, they can generate malware tailored to the specific configuration of the target’s network architecture, such as important files, administrative accounts, and critical systems. The TXT files contain instructions on how to execute the password-protected files.

IT Security Guru
JANUARY 26, 2024
Regular security assessment and penetration testing can also be carried out to identify potential vulnerabilities that, if exploited by cyber threats, may compromise the systems of vehicles.

The Last Watchdog
AUGUST 19, 2021
This is the type of incident that could have been identified as a risk by a properly scoped penetration test and detected with the use of internal network monitoring tools. Most of the modern attacks use evasive malware that are built to work under the radar. Jack Chapman, VP of Threat Intelligence, Egress.
NopSec
NOVEMBER 15, 2022
With NopSec, your vulnerability risk scores are reprioritized based on insights from 30+ threat intelligence feeds for malware, ransomware, threat actors/campaigns, public exploit databases, social media, and more. NopSec brings in your full tech stack for a holistic view into your organization’s unique vulnerability outlook.

SiteLock
OCTOBER 12, 2021
They are also becoming more concerned about how the provider monitors security events, responds to malware attacks , and reports on these issues. David Balaban is a computer security researcher with over 17 years of experience in malware analysis and antivirus software evaluation. David runs MacSecurity.net.

eSecurity Planet
SEPTEMBER 10, 2021
The following sections speak to how ransomware can affect organizations with backup strategies in place, the implications of advanced malware , and why the type of backup solution matters. Malware constantly evolves to match advancing cybersecurity standards and solutions, and ransomware is no exception. Data Exfiltration.

NopSec
JULY 18, 2017
Web browsers most common vulnerabilities and missing patches are reported. Automated generation of virtual patching rules for various WAF platforms.
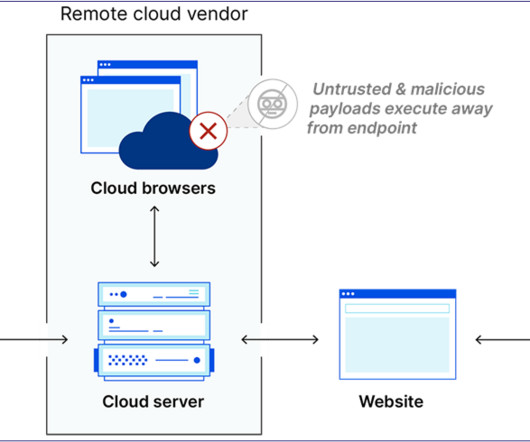
Security Boulevard
JANUARY 17, 2024
Figure 1 — Cloudflare RBI Diagram The primary focus of RBI is to prevent user interactions with web-based malware such as cross-site scripting (XSS), drive-by downloads, and various forms of malicious JavaScript. In this function, it does an excellent job. About Us Lance Cain is an Adversary Simulation Senior Consultant with SpecterOps.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content