5 Best VPNs for Social Media in 2024 (Free & Paid VPNs)
Tech Republic Security
MARCH 7, 2024
Which is the best VPN for social media? Use our guide to compare key features, pros, cons, and more.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
MARCH 7, 2024
Which is the best VPN for social media? Use our guide to compare key features, pros, cons, and more.

CSO Magazine
NOVEMBER 3, 2022
A new espionage campaign, dubbed SandStrike, has been detected using malicious VPN apps to load spyware on Android devices, cybersecurity company Kaspersky reports. To read this article in full, please click here
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Malwarebytes
MARCH 11, 2021
Virtual Private Networks ( VPN s) are popular but often misunderstood. VPNs are for illegal activity. Some people think that VPNs are only useful for doing things like torrenting, accessing geo-locked content, or getting around work/school/government firewalls. I don’t need a mobile VPN. My VPN won’t let me watch Netflix.
Security Affairs
DECEMBER 2, 2021
Russia’s internet watchdog, ‘Roskomnadzor’, has announced the ban of other VPN products, 15 VPN services are now illegal in Russia. Russian communications watchdog Roskomnadzor tightens the control over the Internet and blocked access to six more VPN services. SecurityAffairs – hacking, VPN services). Pierluigi Paganini.

SiteLock
AUGUST 27, 2021
Setting up a VPN can ensure your data is safe when you’re not using a trusted connection by encrypting data as it’s transmitted across shared or public networks, keeping your sensitive information from being exposed. What to Look for in a VPN. The first feature to look for in a VPN is military-grade (256-bit) encryption.

Hot for Security
FEBRUARY 16, 2021
A virtual private network (VPN) provides anonymity and digital privacy by creating a secure and private tunnel between the user and the online destinations he visits. A VPN encrypts computer traffic, masking your IP address and location, preventing snoopers or hackers from viewing or intercepting your data. Netflix and chill anywhere.

SecureBlitz
MAY 19, 2021
If you are looking for the best VPN for Nigeria, this post reveals the best options. Also, in the end, we will reveal the VPN service providers that have VPN servers in Nigeria. VPN in Nigeria is a must-use based on the recent clamor of Nigeria’s ruling political class to regulate social media usage by.

The Hacker News
JUNE 18, 2021
Russia's telecommunications and media regulator Roskomnadzor (RKN) on Thursday introduced restrictions on the operation of VyprVPN and Opera VPN services in the country. "In

Malwarebytes
APRIL 11, 2022
A credential-stealing Windows-based malware, Spyware.FFDroider , is after social media credentials and cookies, according to researchers at ThreatLabz. The malware also plans to steal saved VPN/dial up credentials from the AppdataMicrosoftNetworkConnectionsPbkrasphone.pbk and Pbkrasphone.pbk phonebooks if present. Social media.

Malwarebytes
MAY 24, 2021
In just the past year, free VPN for Android apps have exposed the data of as many as 41 million users, revealing consumers’ email addresses, payment information, clear text passwords, device IDs, and more. All these people that work on [the VPN service], nobody is going to do it for free. There is no best free VPN for Android.

CyberSecurity Insiders
FEBRUARY 16, 2021
Published in collaboration with the Cybersecurity Insiders, the report includes findings from a global survey of more than 350 cybersecurity professionals on the current state of remote access environments, the rise in VPN vulnerabilities, and the role zero-trust security models play in providing access to enterprise applications.

Identity IQ
APRIL 22, 2021
If you want to help secure your digital identity, a virtual private network (VPN) is a great tool you can use for added online privacy. In this guide, we discuss VPNs in detail, including how they work, how they protect you and why you should use one when browsing the web. What is a VPN? How does a VPN Work?

Malwarebytes
FEBRUARY 27, 2021
VPNs have been a subject of deliberation for a long time. I think the pandemic has made it clear that, yes, using a VPN is useful, even necessary, most especially for those working remotely. We’re going to take a look at free VPNs and paid VPNs in general. The honest free VPN. The mystery free VPN.

SC Magazine
APRIL 8, 2021
Kaspersky reported how recent attacks against a series of European industrial networks were accomplished at a vulnerability in Fortinet’s FortiGate VPN. Kaspersky is the first to report how those attacks were accomplished: a vulnerability in Fortinet’s FortiGate VPN. Alexxsun / CC BY-SA 4.0 ).

Approachable Cyber Threats
SEPTEMBER 30, 2021
You can’t access that app someone mentioned, so you ask them and they tell you to “just use the VPN.” And why can you access the app after using the VPN, but you couldn’t before? A Virtual Private Network, or VPN, is a technology that allows you to connect your device to another IT network. This is where a VPN comes in.

Security Affairs
JULY 13, 2021
NetBlocks reported partial disruption to social media and messaging platforms in Cuba from 12 July 2021 shortly after Cubans went to the streets to protest the government. VPN services have yet to be blocked in the country, allowing citizens to bypass internet censorship. Follow me on Twitter: @securityaffairs and Facebook.

Malwarebytes
MARCH 29, 2021
In addition, we speak to Malwarebytes senior security researcher JP Taggart about the importance of trusting your VPN. But obscuring your Internet activity—including the websites you visit, the searches you make, the files you download—doesn’t mean that a VPN magically disappears those things. Source: ComputerWeekly).

Joseph Steinberg
MAY 9, 2022
According to a report published by The Washington Post , downloads by Russians of the 10 most popular VPN applications jumped from fewer than 15,000 per day just before the Russian invasion of Ukraine to a current figure of over 300,000 a day – even reaching as high as 475,000 per day at one point during the current military campaign.

Security Affairs
JANUARY 18, 2022
Some administrators and users reported problems with L2TP VPN connections on Windows 10 after installing the recent Windows 10 and Windows 11 cumulative updates. The post Microsoft releases Windows out-of-band emergency fixes for Win Server, VPN issues appeared first on Security Affairs. Pierluigi Paganini.

SC Magazine
MAY 28, 2021
FireEye Mandiant, working in in tandem with the Cybersecurity and Infrastructure Security Agency and Ivanti, reported details of 16 malware families exclusively designed to infect Ivanti Pulse Connect Secure VPN appliances, and used by several cyber espionage groups believed to be affiliated with the Chinese government.

Krebs on Security
JULY 18, 2022
911 says its network is made up entirely of users who voluntarily install its “free VPN” software. Residential proxy services are often marketed to people seeking the ability to evade country-specific blocking by the major movie and media streaming providers. “The free VPN apps, and the other is trojanized torrents.
SiteLock
AUGUST 27, 2021
Now, think about how many times you have checked your bank account or logged into your social media on a public Wi-Fi connection. This is why using a VPN for secure browsing can help protect your data while using public network. SiteLock VPN makes securing your connection easy! What is a virtual private network (VPN)?

Krebs on Security
AUGUST 19, 2020
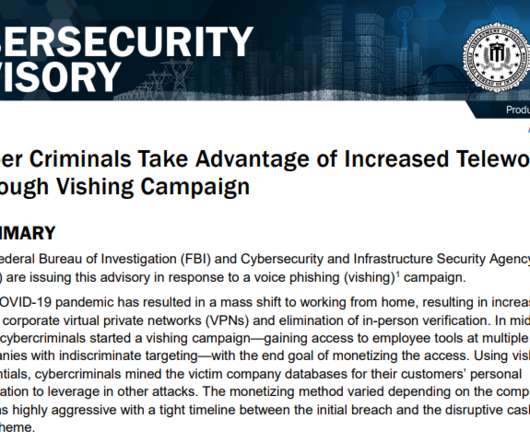
But one increasingly brazen group of crooks is taking your standard phishing attack to the next level, marketing a voice phishing service that uses a combination of one-on-one phone calls and custom phishing sites to steal VPN credentials from employees. The employee phishing page bofaticket[.]com. Image: urlscan.io. ” SPEAR VISHING.

Security Affairs
JANUARY 17, 2020
Chinese authorities continue operations against unauthorized VPN services that are very popular in the country. China continues to intensify the monitoring of the cyberspace applying and persecution of VPN services that could be used to bypass its censorship system known as the Great Firewall. Pierluigi Paganini.
Krebs on Security
AUGUST 21, 2020
The advisory came less than 24 hours after KrebsOnSecurity published an in-depth look at a crime group offering a service that people can hire to steal VPN credentials and other sensitive data from employees working remotely during the Coronavirus pandemic. authenticate the phone call before sensitive information can be discussed.

Krebs on Security
NOVEMBER 2, 2021
.” In the first week of September, Groove posted on its darknet blog nearly 500,000 login credentials for customers of Fortinet VPN products, usernames and passwords that could be used to remotely connect to vulnerable systems. “It’s so funny to read Twitter and the news these days But the result is great so far.

Dark Reading
NOVEMBER 2, 2022
"SandStrike," the latest example of espionage-aimed Android malware, relies on elaborate social media efforts and back-end infrastructure.

Troy Hunt
APRIL 17, 2018
Often, you'll see this pattern play out ad nauseam as the organisation involved takes the shotgun approach of blasting their message out over and over again: When you look for a VPN, you really want to be confident they're responsible, ethical and behave in a professional manner. link] — Troy Hunt (@troyhunt) April 12, 2018.

CyberSecurity Insiders
APRIL 18, 2021
As of now, the alliance has approved mobile apps and Virtual Private Network (VPN) services and is planning to include all cloud connected services like social media apps in near future. Google’s Pixel series of phones 4, XL and 4a became the first devices to pass through the IOT certification last year.

CyberSecurity Insiders
MAY 4, 2023
3. Use a VPN: A Virtual Private Network (VPN) encrypts your internet traffic, making it difficult for anyone to spy on your online activities. A VPN also allows you to access geo-restricted content and protect your online identity. If you must use public Wi-Fi, use a VPN to encrypt your traffic.
Security Affairs
AUGUST 28, 2023
According to 404 Media , Yossi reported the issue to Microsoft earlier this month, but it seems that the company initially downplayed the problem and gave no indication that it plans to address the flaw. “[the] However, after 404 Media contacted Microsoft for comment, the IT giant announced it plans to fix the problem in an upcoming update.

CyberSecurity Insiders
JUNE 5, 2023
From social media platforms to online shopping and banking, we share a wealth of personal information that can be vulnerable to misuse or exploitation. Enable 2FA whenever available, especially for sensitive accounts like email, banking, and social media. This helps prevent unauthorized access even if your password is compromised.

Security Affairs
NOVEMBER 2, 2022
The threat actors were distributing a VPN app embedding a highly sophisticated spyware. The attackers set up Facebook and Instagram accounts with more than 1,000 followers and designed attractive religious-themed graphic materials in order to trick victims into downloading the tainted VPN app. í religion that are banned in Iran.

Malwarebytes
FEBRUARY 28, 2023
The remote developer’s PC was reportedly compromised via a remote code execution vulnerability in a third-party media player, which was exploited to deploy a keylogger. Or, put another way, LastPass allowing an employee to use a computer with a vulnerable media player for work. Use a VPN to connect to the office network.

Security Affairs
FEBRUARY 12, 2024
Also, consider using a Virtual Private Network (VPN) to encrypt your data and make it unreadable to hackers. Invest in a VPN to encrypt your data and ensure websites you use have SSL/TSL certificates (look for “https” in the URL). Use a VPN to encrypt your internet traffic and avoid connecting to unfamiliar Wi-Fi networks.

Security Affairs
JUNE 12, 2023
The researcher describes the issue as a reachable pre-authentication that impacts every SSL VPN appliance. This is reachable pre-authentication, on every SSL VPN appliance. “A new critical flaw, not made public at this stage, concerns Fortinet on its Fortigate firewalls, more specifically the SSL VPN functionalities.”

Identity IQ
MARCH 11, 2021
Use a VPN . A virtual private network (VPN) essentially creates an encrypted virtual tunnel between your computer and another server anywhere in the world. When using a VPN, your IP address is disguised and your connection is secure against external attacks. Avoid Oversharing on Social Media.

Security Affairs
JANUARY 23, 2021
The company was targeted with a coordinated attack on its internal systems, threat actors exploited zero-day vulnerabilities in their VPN solutions, such as NetExtender VPN client version 10.x Below the list of affected products shared by THN: NetExtender VPN client version 10.x x and Secure Mobile Access ( SMA ).

Krebs on Security
NOVEMBER 21, 2020
The phishers often will explain that they’re calling from the employer’s IT department to help troubleshoot issues with the company’s email or virtual private networking (VPN) technology. Restrict VPN access hours, where applicable, to mitigate access outside of allowed times.

The Last Watchdog
JANUARY 3, 2023
With the rise in social media, criminals have more platforms with which to target potential phishing victims. Since many people use the same passwords across social media platforms and for sites for banks or credit cards, a criminal needs access to just one account to gain access to every account.

Hot for Security
JUNE 22, 2021
If you do, chose password-protected networks and use a VPN to prevent eavesdropping on online activity Resist the urge to post on social media platforms about your activity and location. Avoid connecting to free public Wi-Fi s in restaurants, airports, cafes or hotels.

Adam Levin
NOVEMBER 15, 2019
News that Virtual Private Network ( VPN ) provider NordVPN was breached spread quickly. While the breach of a major VPN service is newsworthy, this one wasn’t particularly. But one of the watchwords of good cyber hygiene, a VPN, was breached. Who Is Using VPNs? The incident put NordVPN in the hot seat.

Security Affairs
APRIL 28, 2023
through 4.73, VPN series firmware versions 4.60 through 5.35, USG20(W)-VPN firmware versions 4.16 through 5.35, and VPN series firmware versions 4.30 Researchers from TRAPA Security have discovered a critical remote code execution vulnerability, tracked as CVE-2023-28771 (CVSS score 9.8), impacting Zyxel Firewall. through 5.35.

Krebs on Security
FEBRUARY 14, 2022
Wazawaka has since “lost his mind” according to his erstwhile colleagues, creating a Twitter account to drop exploit code for a widely-used virtual private networking (VPN) appliance, and publishing bizarre selfie videos taunting security researchers and journalists. Wazawaka, a.k.a. Matveev, a.k.a. “Orange,” a.k.a.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content