10 Top Open Source Penetration Testing Tools
eSecurity Planet
FEBRUARY 24, 2022
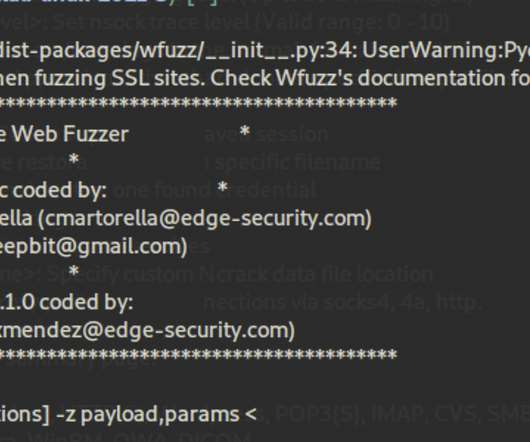
Such security audits require various techniques and tools to simulate classic steps of an attack, such as information gathering (reconnaissance), phishing, or privilege escalation. Vulnerability management solutions. Patch management software. Basic phishing modules will hardly work with cybersecurity-aware employees.
















Let's personalize your content